Citrix Hypervisor
Virtual GPU Software R418 for Citrix Hypervisor Release Notes
Release information for all users of NVIDIA virtual GPU software and hardware on Citrix Hypervisor.
These Release Notes summarize current status, information on validated platforms, and known issues with NVIDIA vGPU software and associated hardware on Citrix Hypervisor.
1.1. NVIDIA vGPU Software Driver Versions
Each release in this release family of NVIDIA vGPU software includes a specific version of the NVIDIA Virtual GPU Manager, NVIDIA Windows driver, and NVIDIA Linux driver.
| NVIDIA vGPU Software Version | NVIDIA Virtual GPU Manager Version | NVIDIA Windows Driver Version | NVIDIA Linux Driver Version |
|---|---|---|---|
| 8.10 | 418.240 | 427.71 | 418.240 |
| 8.9 | 418.226.00 | 427.60 | 418.226.00 |
| 8.8 | 418.213 | 427.48 | 418.211.00 |
| 8.7 | 418.196 | 427.33 | 418.197.02 |
| 8.6 | 418.181 | 427.11 | 418.181.07 |
| 8.5 | 418.165.01 | 426.94 | 418.165.01 |
| 8.4 | 418.149 | 426.72 | 418.149 |
| 8.3 | 418.130 | 426.52 | 418.130 |
| 8.2 | 418.109 | 426.26 | 418.109 |
| 8.1 | 418.92 | 426.04 | 418.92 |
| 8.0 | 418.66 | 425.31 | 418.70 |
For details of which Citrix Hypervisor releases are supported, see Hypervisor Software Releases.
1.2. Compatibility Requirements for the NVIDIA vGPU Manager and Guest VM Driver
The releases of the NVIDIA vGPU Manager and guest VM drivers that you install must be compatible. If you install an incompatible guest VM driver release for the release of the vGPU Manager that you are using, the NVIDIA vGPU fails to load. See VM running older NVIDIA vGPU drivers fails to initialize vGPU when booted.
Different versions of the vGPU Manager and guest VM driver from within the same main release branch can be used together. For example, you can use the vGPU Manager from release 8.1 with guest VM drivers from release 8.0. However, versions of the vGPU Manager and guest VM driver from different main release branches cannot be used together. For example, you cannot use the vGPU Manager from release 8.1 with guest VM drivers from release 7.2.
This requirement does not apply to the NVIDIA vGPU software license server. All releases in this release family of NVIDIA vGPU software are compatible with all releases of the license server.
1.3. Updates in Release 8.10
New Features in Release 8.10
- Security updates - see Security Bulletin: NVIDIA GPU Display Driver - February 2022, which is posted shortly after the release date of this software and is listed on the NVIDIA Product Security page
- Miscellaneous bug fixes
Hardware and Software Support Introduced in Release 8.10
- Support for Red Hat Enterprise Linux 8.5 as a guest OS
Feature Support Withdrawn in Release 8.10
- Red Hat Enterprise Linux 8.1 is no longer supported as a guest OS.
- Red Hat Enterprise Linux 7.8. and 7.7 are no longer supported as a guest OS.
1.4. Updates in Release 8.9
New Features in Release 8.9
- Security updates - see Security Bulletin: NVIDIA GPU Display Driver - October 2021, which is posted shortly after the release date of this software and is listed on the NVIDIA Product Security page
- Miscellaneous bug fixes
1.5. Updates in Release 8.8
New Features in Release 8.8
- Security updates - see Security Bulletin: NVIDIA GPU Display Driver - July 2021
- Miscellaneous bug fixes
Hardware and Software Support Introduced in Release 8.8
- Support for Red Hat Enterprise Linux 8.4 as a guest OS
Feature Support Withdrawn in Release 8.8
- Citrix Hypervisor 7.0 is no longer supported.
1.6. Updates in Release 8.7
New Features in Release 8.7
- Security updates - see Security Bulletin: NVIDIA GPU Display Driver - April 2021
- Miscellaneous bug fixes
1.7. Updates in Release 8.6
New Features in Release 8.6
- Security updates - see Security Bulletin: NVIDIA GPU Display Driver - January 2021
- Miscellaneous bug fixes
Feature Support Withdrawn in Release 8.6
- Red Hat Enterprise Linux 7.6 is no longer supported as a guest OS
1.8. Updates in Release 8.5
New Features in Release 8.5
- Security updates- see Security Bulletin: NVIDIA GPU Display Driver - September 2020
- Miscellaneous bug fixes
Feature Support Withdrawn in Release 8.5
- Citrix Hypervisor 8.0 is no longer supported.
As a result of the withdrawal of support for Citrix Hypervisor 8.0, the following features are withdrawn on Citrix Hypervisor:
- Support for the Tesla T4 GPU
- Support for XenMotion with vGPU
- Support for the following releases as a guest OS:
- Red Hat Enterprise Linux 8.2 and 8.1
- CentOS Linux 8 (1911)
1.9. Updates in Release 8.4
New Features in Release 8.4
- Miscellaneous bug fixes
- Security updates - see Security Bulletin: NVIDIA GPU Display Driver - June 2020
Hardware and Software Support Introduced in Release 8.4
- Support for the following guest OS releases
- Red Hat Enterprise Linux 8.2 and 7.8
- CentOS 7.8
Feature Support Withdrawn in Release 8.4
- The following OS releases are no longer supported as a guest OS:
- Red Hat Enterprise Linux 7.5
- CentOS 7.5
1.10. Updates in Release 8.3
New Features in Release 8.3
- Miscellaneous bug fixes
- Security updates - see Security Bulletin: NVIDIA GPU Display Driver - February 2020
Hardware and Software Support Introduced in Release 8.3
- Support for the following guest OS releases
- Red Hat Enterprise Linux 8.1
- CentOS Linux 8 (1911)
- Support for Citrix Virtual Apps and Desktops version 7 1912
Feature Support Withdrawn in Release 8.3
- Citrix Hypervisor 7.6 is no longer supported.
- The following OS releases are no longer supported as a guest OS:
- Windows Server 2008 R2
- Red Hat Enterprise Linux 7.0-7.4
- CentOS 7.0-7.4
1.11. Updates in Release 8.2
New Features in Release 8.2
- Miscellaneous bug fixes
- Security updates - see Security Updates
Hardware and Software Support Introduced in Release 8.2
- Support for Citrix Virtual Apps and Desktops version 7 1909
1.12. Updates in Release 8.1
New Features in Release 8.1
- Security updates
- Miscellaneous bug fixes
Hardware and Software Support Introduced in Release 8.1
- Support for Red Hat Enterprise Linux 7.7 as a guest OS
- Support for Citrix Virtual Apps and Desktops version 7 1906
1.13. Updates in Release 8.0
New Features in Release 8.0
- New -1B4 virtual GPU types
- XenMotion support on the following GPUs:
- Tesla V100 SXM2
- Tesla V100 SXM2 32GB
- Tesla V100 PCIe
- Tesla V100 PCIe 32GB
- Tesla V100 FHHL
- Quadro RTX 6000
- Quadro RTX 8000
For the complete list of GPUs that support XenMotion, see XenMotion with vGPU Support.
- XenMotion support on Citrix Hypervisor 8.0
- Security updates
- Miscellaneous bug fixes
Hardware and Software Support Introduced in Release 8.0
- Support for the following GPUs:
- Quadro RTX 6000
- Quadro RTX 8000
- Support for Citrix Hypervisor 8.0
- Support for the following OS releases as a guest OS:
- Windows 10 October 2018 Update (1809)
- Windows Server 2019
Feature Support Withdrawn in Release 8.0
- Citrix Hypervisor 7.5 is no longer supported.
This release family of NVIDIA vGPU software provides support for several NVIDIA GPUs on validated server hardware platforms, Citrix Hypervisor hypervisor software versions, and guest operating systems. It also supports the version of NVIDIA CUDA Toolkit that is compatible with R418 drivers.
2.1. Supported NVIDIA GPUs and Validated Server Platforms
This release of NVIDIA vGPU software provides support for the following NVIDIA GPUs on Citrix Hypervisor, running on validated server hardware platforms:
- GPUs based on the NVIDIA Maxwell™ graphic architecture:
- Tesla M6
- Tesla M10
- Tesla M60
- GPUs based on the NVIDIA Pascal™ architecture:
- Tesla P4
- Tesla P6
- Tesla P40
- Tesla P100 PCIe 16 GB (XenMotion with vGPU is not supported.)
- Tesla P100 SXM2 16 GB (XenMotion with vGPU is not supported.)
- Tesla P100 PCIe 12GB (XenMotion with vGPU is not supported.)
- GPUs based on the NVIDIA Volta architecture:
- Tesla V100 SXM2
- Tesla V100 SXM2 32GB
- Tesla V100 PCIe
- Tesla V100 PCIe 32GB
- Tesla V100 FHHL
- GPUs based on the NVIDIA Turing architecture:
- 8.0-8.4 only: Tesla T4
- Quadro RTX 6000 in displayless mode (GRID Virtual PC and GRID Virtual Applications are not supported.)
- Quadro RTX 8000 in displayless mode (GRID Virtual PC and GRID Virtual Applications are not supported.)
In displayless mode, local physical display connectors are disabled.
For a list of validated server platforms, refer to NVIDIA GRID Certified Servers.
Tesla M60 and M6 GPUs support compute mode and graphics mode. NVIDIA vGPU requires GPUs that support both modes to operate in graphics mode.
Recent Tesla M60 GPUs and M6 GPUs are supplied in graphics mode. However, your GPU might be in compute mode if it is an older Tesla M60 GPU or M6 GPU, or if its mode has previously been changed.
To configure the mode of Tesla M60 and M6 GPUs, use the gpumodeswitch tool provided with NVIDIA vGPU software releases.
2.2. Hypervisor Software Releases
Changes to Citrix Product Names and Release Numbers
Citrix has changed the product names of its hypervisor and virtual desktop software.
| Old Name | New Name |
|---|---|
| XenServer | Citrix Hypervisor |
| XenApp and XenDesktop | Citrix Virtual Apps and Desktops |
| Citrix Receiver | Citrix Workspace App |
The release number of Citrix Virtual Apps and Desktops releases after 7.18 is in the form 7 yymm, where yymm denotes the year and month that the product was released. For example, for a product released in August 2018, yymm is 1808.
For more information, see these topics in the Citrix documentation:
Supported Citrix Hypervisor Releases
This release family of NVIDIA vGPU software is supported on the Citrix Hypervisor releases listed in the table.Support for NVIDIA vGPU software requires the Premium Edition (previously Enterprise Edition) of Citrix Hypervisor. For details, see Licensing in the Citrix documentation.
Cumulative update releases for a base release of Citrix Hypervisor are compatible with the base release and can also be used with this version of NVIDIA vGPU software unless expressly stated otherwise.
| Software | Releases Supported | Notes |
|---|---|---|
| 8.0-8.4 only: Citrix Hypervisor 8.0 |
RTM build and compatible cumulative update releases |
In NVIDIA vGPU mode, all NVIDIA GPUs that support NVIDIA vGPU software are supported. In GPU pass-through mode, the following GPUs are not supported:
This release supports XenMotion with vGPU on suitable GPUs as listed in Supported NVIDIA GPUs and Validated Server Platforms. |
| 8.0-8.2 only: Citrix XenServer 7.6 |
RTM build and compatible cumulative update releases |
All NVIDIA GPUs that support NVIDIA vGPU software are supported. This release supports XenMotion with vGPU on suitable GPUs as listed in Supported NVIDIA GPUs and Validated Server Platforms. |
| Citrix XenServer 7.1 |
RTM build and compatible cumulative update releases |
Not supported on Tesla T4. XenMotion with vGPU is not supported. |
| 8.0-8.7 only: Citrix XenServer 7.0 |
RTM build 125380 and compatible cumulative update releases |
Not supported on Tesla T4. XenMotion with vGPU is not supported. |
Supported Virtual Desktop Software Releases
This release supports only the virtual desktop software releases listed in the table. Except where otherwise stated, HDX 3D Pro mode is supported but not required.| Software | Releases Supported |
|---|---|
| Citrix Virtual Apps and Desktops |
Since 8.3: Versions 7 1912, 7 1909, 7 1906, 7 1903, and 7 1808 8.2 only: Versions 7 1909, 7 1906, 7 1903, and 7 1808 8.1 only: Versions 7 1906, 7 1903, and 7 1808 8.0 only: Versions 7 1903 and 7 1808 |
| XenApp/XenDesktop |
Versions 7.18 and 7.17 Version 7.15 in HDX 3D Pro mode (required to ensure that the NVIDIA GPU can be used unrestricted) |
2.3. Guest OS Support
NVIDIA vGPU software supports several Windows releases and Linux distributions as a guest OS. The supported guest operating systems depend on the hypervisor software version.
Use only a guest OS release that is listed as supported by NVIDIA vGPU software with your virtualization software. To be listed as supported, a guest OS release must be supported not only by NVIDIA vGPU software, but also by your virtualization software. NVIDIA cannot support guest OS releases that your virtualization software does not support.
NVIDIA vGPU software supports only 64-bit guest operating systems. No 32-bit guest operating systems are supported. In GPU pass-through mode, the following GPUs are not supported on Citrix Hypervisor 8.0:
- Quadro RTX 6000
- Quadro RTX 8000
2.3.1. Windows Guest OS Support
NVIDIA vGPU software supports only the 64-bit Windows releases listed in the table as a guest OS on Citrix Hypervisor. The releases of Citrix Hypervisor for which a Windows release is supported depend on whether NVIDIA vGPU or pass-through GPU is used.If a specific release, even an update release, is not listed, it’s not supported.
XenMotion with vGPU is supported on supported Windows guest OS releases.
| Guest OS | NVIDIA vGPU - Citrix Hypervisor Releases | Pass-Through GPU - Citrix Hypervisor Releases |
|---|---|---|
| Windows Server 2019 | Since 8.5: 7.1 cumulative update 2 8.0-8.4 only: 8.0, 7.1 cumulative update 2 |
Since 8.5: 7.1 cumulative update 2 8.0-8.4 only: 8.0, 7.1 cumulative update 2 |
| Windows Server 2016 1709, 1607 | Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
| Windows Server 2012 R2 | Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
| 8.0-8.2 only: Windows Server 2008 R2 | 8.0, 7.6, 7.1, 7.0 |
8.0, 7.6, 7.1, 7.0 Supported only on GPUs based on the Maxwell architecture |
| Windows 10 October 2018 Update (1809) and all Windows 10 releases supported by Microsoft up to and including this release | Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
| Windows 8.1 Update | Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
| Windows 8.1 | Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
- |
| Windows 8 | Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
- |
| Windows 7 | Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 Supported only on GPUs based on the Maxwell architecture |
2.3.2. Linux Guest OS Support
NVIDIA vGPU software supports only the Linux distributions listed in the table as a guest OS on Citrix Hypervisor. The releases of Citrix Hypervisor for which a Linux release is supported depend on whether NVIDIA vGPU or pass-through GPU is used.If a specific release, even an update release, is not listed, it’s not supported.
XenMotion with vGPU is not supported on any Linux guest OS release.
| Guest OS | NVIDIA vGPU - Citrix Hypervisor Releases | Pass-Through GPU - Citrix Hypervisor Releases |
|---|---|---|
| Since 8.4: Red Hat Enterprise Linux 8.2 | 8.4 only: 8.0 |
8.4 only: 8.0 |
| 8.3, 8.4 only: Red Hat Enterprise Linux 8.1 | 8.0 |
8.0 |
| 8.3, 8.4 only: CentOS Linux 8 (1911) | 8.0 |
8.0 |
| 8.6-8.9 only: Red Hat Enterprise Linux 7.7-7.8 | 8.8, 8.9 only: 7.1 8.0-8.7 only: 7.1, 7.0 |
8.8, 8.9 only: 7.1 8.0-8.7 only: 7.1, 7.0 |
| 8.4, 8.5 only: Red Hat Enterprise Linux 7.6-7.8 | 8.5 only: 7.1, 7.0 8.4 only: 8.0, 7.1, 7.0 |
8.5 only: 7.1, 7.0 8.4 only: 8.0, 7.1, 7.0 |
| 8.3 only: Red Hat Enterprise Linux 7.5-7.7 | 8.0, 7.1, 7.0 |
8.0, 7.1, 7.0 |
| 8.1, 8.2 only: Red Hat Enterprise Linux 7.0-7.7 | 8.0, 7.6, 7.1, 7.0 |
8.0, 7.6, 7.1, 7.0 |
| 8.0 only: Red Hat Enterprise Linux 7.0-7.6 | 8.0, 7.6, 7.1, 7.0 |
8.0, 7.6, 7.1, 7.0 |
| Since 8.6: CentOS 7.7-7.8 | Since 8.8: 7.1 8.6, 8.7 only: 7.1, 7.0 |
Since 8.8: 7.1 8.6, 8.7 only: 7.1, 7.0 |
| 8.4, 8.5 only: CentOS 7.6-7.8 | 8.5 only: 7.1, 7.0 8.4 only: 8.0, 7.1, 7.0 |
8.5 only: 7.1, 7.0 8.4 only: 8.0, 7.1, 7.0 |
| 8.3 only: CentOS 7.5, 7.6 | 8.0, 7.1, 7.0 |
8.0, 7.1, 7.0 |
| 8.0-8.2 only: CentOS 7.0-7.6 | 8.0, 7.6, 7.1, 7.0 |
8.0, 7.6, 7.1, 7.0 |
| Ubuntu 18.04 LTS | 8.3, 8.4 only: 8.0 8.0-8.2 only: 8.0, 7.6 |
8.3, 8.4 only: 8.0 8.0-8.2 only: 8.0, 7.6 |
| Ubuntu 16.04 LTS | Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
| Ubuntu 14.04 LTS | Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
Since 8.8: 7.1 8.5-8.7 only: 7.1, 7.0 8.3, 8.4 only: 8.0, 7.1, 7.0 8.0-8.2 only: 8.0, 7.6, 7.1, 7.0 |
2.4. NVIDIA CUDA Toolkit Version Support
The releases in this release family of NVIDIA vGPU software support NVIDIA CUDA Toolkit 10.1.
For more information about NVIDIA CUDA Toolkit, see CUDA Toolkit 10.1 Documentation. This documentation applies to the base NVIDIA CUDA Toolkit 10.1 release and updates to the base release.
If you are using NVIDIA vGPU software with CUDA on Linux, avoid conflicting installation methods by installing CUDA from a distribution-independent runfile package. Do not install CUDA from a distribution-specific RPM or Deb package.
To ensure that the NVIDIA vGPU software graphics driver is not overwritten when CUDA is installed, deselect the CUDA driver when selecting the CUDA components to install.
For more information, see NVIDIA CUDA Installation Guide for Linux.
2.5. XenMotion with vGPU Support
XenMotion with vGPU is supported only on a subset of supported GPUs, Citrix Hypervisor releases, and guest operating systems. Supported GPUs:
- Tesla M6
- Tesla M10
- Tesla M60
- Tesla P4
- Tesla P6
- Tesla P40
- Tesla V100 SXM2
- Tesla V100 SXM2 32GB
- Tesla V100 PCIe
- Tesla V100 PCIe 32GB
- Tesla V100 FHHL
- 8.0-8.4 only: Tesla T4
- Quadro RTX 6000
- Quadro RTX 8000
Supported Citrix Hypervisor releases:
- 8.3, 8.4 only: 8.0 only
- 8.0-8.2 only: 8.0 and 7.6 only
As a result of the withdrawal of support for Citrix Hypervisor 8.0 and 7.6, XenMotion with vGPU is supported only on NVIDIA vGPU software releases 8.0-8.4.
Supported guest OS releases: Windows only. XenMotion with vGPU is not supported on Linux.
Known product limitations for this release of NVIDIA vGPU software are described in the following sections.
3.1. Issues occur when the channels allocated to a vGPU are exhausted
Description
Issues occur when the channels allocated to a vGPU are exhausted and the guest VM to which the vGPU is assigned fails to allocate a channel to the vGPU. A physical GPU has a fixed number of channels and the number of channels allocated to each vGPU is inversely proportional to the maximum number of vGPUs allowed on the physical GPU.
When the channels allocated to a vGPU are exhausted and the guest VM fails to allocate a channel, the following errors are reported on the hypervisor host or in an NVIDIA bug report:
Jun 26 08:01:25 srvxen06f vgpu-3[14276]: error: vmiop_log: (0x0): Guest attempted to allocate channel above its max channel limit 0xfb
Jun 26 08:01:25 srvxen06f vgpu-3[14276]: error: vmiop_log: (0x0): VGPU message 6 failed, result code: 0x1a
Jun 26 08:01:25 srvxen06f vgpu-3[14276]: error: vmiop_log: (0x0): 0xc1d004a1, 0xff0e0000, 0xff0400fb, 0xc36f,
Jun 26 08:01:25 srvxen06f vgpu-3[14276]: error: vmiop_log: (0x0): 0x1, 0xff1fe314, 0xff1fe038, 0x100b6f000, 0x1000,
Jun 26 08:01:25 srvxen06f vgpu-3[14276]: error: vmiop_log: (0x0): 0x80000000, 0xff0e0200, 0x0, 0x0, (Not logged),
Jun 26 08:01:25 srvxen06f vgpu-3[14276]: error: vmiop_log: (0x0): 0x1, 0x0
Jun 26 08:01:25 srvxen06f vgpu-3[14276]: error: vmiop_log: (0x0): , 0x0
Workaround
Use a vGPU type with more frame buffer, thereby reducing the maximum number of vGPUs allowed on the physical GPU. As a result, the number of channels allocated to each vGPU is increased.
3.2. Total frame buffer for vGPUs is less than the total frame buffer on the physical GPU
Some of the physical GPU's frame buffer is used by the hypervisor on behalf of the VM for allocations that the guest OS would otherwise have made in its own frame buffer. The frame buffer used by the hypervisor is not available for vGPUs on the physical GPU. In NVIDIA vGPU deployments, frame buffer for the guest OS is reserved in advance, whereas in bare-metal deployments, frame buffer for the guest OS is reserved on the basis of the runtime needs of applications.
The approximate amount of frame buffer that NVIDIA vGPU software reserves can be calculated from the following formula:
max-reserved-fb = vgpu-profile-size-in-mb÷16 + 16
- max-reserved-fb
- The maximum total amount of reserved frame buffer in Mbytes that is not available for vGPUs.
- vgpu-profile-size-in-mb
- The amount of frame buffer in Mbytes allocated to a single vGPU. This amount depends on the vGPU type. For example, for the T4-16Q vGPU type, vgpu-profile-size-in-mb is 16384.
In VMs running a Windows guest OS that supports Windows Display Driver Model (WDDM) 1.x, namely, Windows 7, Windows 8.1, Windows Server 2008, and Windows Server 2012, an additional 48 Mbytes of frame buffer are reserved and not available for vGPUs.
3.3. Issues may occur with graphics-intensive OpenCL applications on vGPU types with limited frame buffer
Description
Issues may occur when graphics-intensive OpenCL applications are used with vGPU types that have limited frame buffer. These issues occur when the applications demand more frame buffer than is allocated to the vGPU.
For example, these issues may occur with the Adobe Photoshop and LuxMark OpenCL Benchmark applications:
- When the image resolution and size are changed in Adobe Photoshop, a program error may occur or Photoshop may display a message about a problem with the graphics hardware and a suggestion to disable OpenCL.
- When the LuxMark OpenCL Benchmark application is run, XID error 31 may occur.
Workaround
For graphics-intensive OpenCL applications, use a vGPU type with more frame buffer.
3.4. vGPU profiles with 512 Mbytes or less of frame buffer support only 1 virtual display head on Windows 10
Description
To reduce the possibility of memory exhaustion, vGPU profiles with 512 Mbytes or less of frame buffer support only 1 virtual display head on a Windows 10 guest OS.
The following vGPU profiles have 512 Mbytes or less of frame buffer:
- Tesla M6-0B, M6-0Q
- Tesla M10-0B, M10-0Q
- Tesla M60-0B, M60-0Q
Workaround
Use a profile that supports more than 1 virtual display head and has at least 1 Gbyte of frame buffer.
3.5. NVENC requires at least 1 Gbyte of frame buffer
Description
Using the frame buffer for the NVIDIA hardware-based H.264/HEVC video encoder (NVENC) may cause memory exhaustion with vGPU profiles that have 512 Mbytes or less of frame buffer. To reduce the possibility of memory exhaustion, NVENC is disabled on profiles that have 512 Mbytes or less of frame buffer. Application GPU acceleration remains fully supported and available for all profiles, including profiles with 512 MBytes or less of frame buffer. NVENC support from both Citrix and VMware is a recent feature and, if you are using an older version, you should experience no change in functionality.
The following vGPU profiles have 512 Mbytes or less of frame buffer:
- Tesla M6-0B, M6-0Q
- Tesla M10-0B, M10-0Q
- Tesla M60-0B, M60-0Q
Workaround
If you require NVENC to be enabled, use a profile that has at least 1 Gbyte of frame buffer.
3.6. VM running older NVIDIA vGPU drivers fails to initialize vGPU when booted
Description
A VM running a version of the NVIDIA guest VM drivers from a previous main release branch, for example release 4.4, will fail to initialize vGPU when booted on a Citrix Hypervisor platform running the current release of Virtual GPU Manager.
In this scenario, the VM boots in standard VGA mode with reduced resolution and color depth. The NVIDIA virtual GPU is present in Windows Device Manager but displays a warning sign, and the following device status:
Windows has stopped this device because it has reported problems. (Code 43)
Depending on the versions of drivers in use, the Citrix Hypervisor VM’s /var/log/messages log file reports one of the following errors:
- An error message:
vmiop_log: error: Unable to fetch Guest NVIDIA driver information
- A version mismatch between guest and host drivers:
vmiop_log: error: Guest VGX version(1.1) and Host VGX version(1.2) do not match
- A signature mismatch:
vmiop_log: error: VGPU message signature mismatch.
Resolution
Install the current NVIDIA guest VM driver in the VM.
3.7. Virtual GPU fails to start if ECC is enabled
Description
Tesla M60, Tesla M6, and GPUs based on the Pascal GPU architecture, for example Tesla P100 or Tesla P4, support error correcting code (ECC) memory for improved data integrity. Tesla M60 and M6 GPUs in graphics mode are supplied with ECC memory disabled by default, but it may subsequently be enabled using nvidia-smi. GPUs based on the Pascal GPU architecture are supplied with ECC memory enabled.
However, NVIDIA vGPU does not support ECC memory. If ECC memory is enabled, NVIDIA vGPU fails to start. Citrix XenCenter displays the following error message:
An emulator required to run this VM failed to start
The following error is logged in the Citrix Hypervisor host’s /var/log/messages log file:
vmiop_log: error: Initialization: VGX not supported with ECC Enabled.
Resolution
Ensure that ECC is disabled on all GPUs.
Before you begin, ensure that NVIDIA Virtual GPU Manager is installed on your hypervisor.
- Use nvidia-smi to list the status of all GPUs, and check for ECC noted as enabled on GPUs.
# nvidia-smi -q ==============NVSMI LOG============== Timestamp : Tue Dec 19 18:36:45 2017 Driver Version : 384.99 Attached GPUs : 1 GPU 0000:02:00.0 [...] Ecc Mode Current : Enabled Pending : Enabled [...]
- Change the ECC status to off on each GPU for which ECC is enabled.
- If you want to change the ECC status to off for all GPUs on your host machine, run this command:
# nvidia-smi -e 0
- If you want to change the ECC status to off for a specific GPU, run this command:
# nvidia-smi -i id -e 0
id is the index of the GPU as reported by nvidia-smi.
This example disables ECC for the GPU with index
0000:02:00.0.# nvidia-smi -i 0000:02:00.0 -e 0
- If you want to change the ECC status to off for all GPUs on your host machine, run this command:
- Reboot the host.
# shutdown –r now
- Confirm that ECC is now disabled for the GPU.
# nvidia-smi -q ==============NVSMI LOG============== Timestamp : Tue Dec 19 18:37:53 2017 Driver Version : 384.99 Attached GPUs : 1 GPU 0000:02:00.0 [...] Ecc Mode Current : Disabled Pending : Disabled [...]
If you later need to enable ECC on your GPUs, run one of the following commands:
- If you want to change the ECC status to on for all GPUs on your host machine, run this command:
# nvidia-smi -e 1
- If you want to change the ECC status to on for a specific GPU, run this command:
# nvidia-smi -i id -e 1
id is the index of the GPU as reported by nvidia-smi.
This example enables ECC for the GPU with index
0000:02:00.0.# nvidia-smi -i 0000:02:00.0 -e 1
After changing the ECC status to on, reboot the host.
3.8. Single vGPU benchmark scores are lower than pass-through GPU
Description
A single vGPU configured on a physical GPU produces lower benchmark scores than the physical GPU run in pass-through mode.
Aside from performance differences that may be attributed to a vGPU’s smaller frame buffer size, vGPU incorporates a performance balancing feature known as Frame Rate Limiter (FRL). On vGPUs that use the best-effort scheduler, FRL is enabled. On vGPUs that use the fixed share or equal share scheduler, FRL is disabled.
FRL is used to ensure balanced performance across multiple vGPUs that are resident on the same physical GPU. The FRL setting is designed to give good interactive remote graphics experience but may reduce scores in benchmarks that depend on measuring frame rendering rates, as compared to the same benchmarks running on a pass-through GPU.
Resolution
FRL is controlled by an internal vGPU setting. On vGPUs that use the best-effort scheduler, NVIDIA does not validate vGPU with FRL disabled, but for validation of benchmark performance, FRL can be temporarily disabled by specifying frame_rate_limiter=0 in the VM’s platform:vgpu_extra_args parameter:
[root@xenserver ~]# xe vm-param-set uuid=e71afda4-53f4-3a1b-6c92-a364a7f619c2 platform:vgpu_extra_args="frame_rate_limiter=0"
[root@xenserver ~]#
The setting takes effect the next time the VM is started or rebooted.
With this setting in place, the VM’s vGPU will run without any frame rate limit. The FRL can be reverted back to its default setting in one of the following ways:
- Removing the
vgpu_extra_argskey from theplatformparameter - Removing
frame_rate_limiter=0from thevgpu_extra_argskey - Setting
frame_rate_limiter=1. For example:[root@xenserver ~]# xe vm-param-set uuid=e71afda4-53f4-3a1b-6c92-a364a7f619c2 platform:vgpu_extra_args="frame_rate_limiter=1" [root@xenserver ~]#
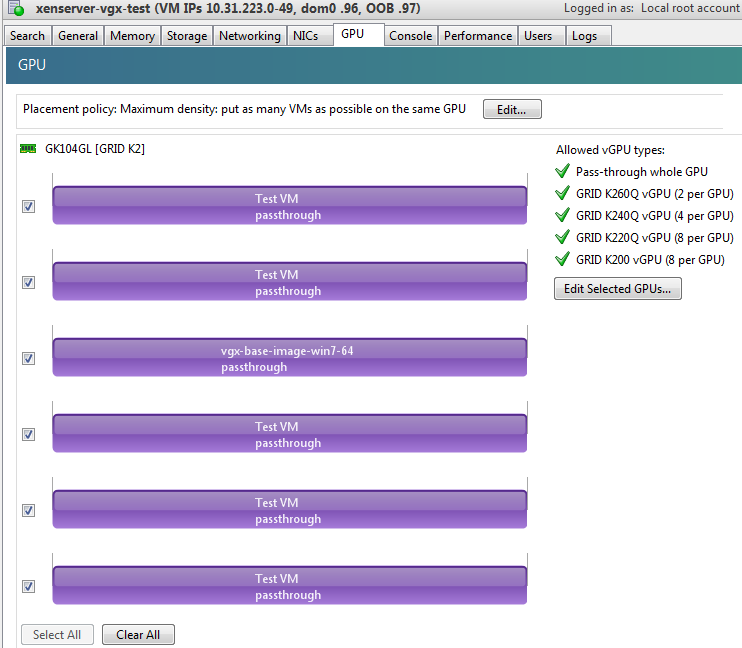
3.9. nvidia-smi fails to operate when all GPUs are assigned to GPU pass-through mode
Description
If all GPUs in the platform are assigned to VMs in pass-through mode, nvidia-smi will return an error:
[root@xenserver-vgx-test ~]# nvidia-smi
Failed to initialize NVML: Unknown Error
This is because GPUs operating in pass-through mode are not visible to nvidia-smi and the NVIDIA kernel driver operating in the Citrix Hypervisordom0.
To confirm that all GPUs are operating in pass-through mode, use XenCenter’s GPU tab to review current GPU assignment:
Resolution
N/A
3.10. Windows Aero is disabled on Citrix Virtual Apps and Desktops session using 3 or 4 monitors in 2560×1600 resolution
Description
Windows Aero may be disabled when Citrix Virtual Apps and Desktops is connected to a VM with a vGPU or passthrough GPU, with 3 or 4 monitors at 2560×1600 resolution.
This limitation is a limitation of Windows 7. For details, see the Microsoft knowledge base article Desktop background disappears with very large extended desktop on Windows 7.
3.11. VMs configured with large memory fail to initialize vGPU when booted
Description
When starting multiple VMs configured with large amounts of RAM (typically more than 32GB per VM), a VM may fail to initialize vGPU. In this scenario, the VM boots in standard VGA mode with reduced resolution and color depth. The NVIDIA vGPU software GPU is present in Windows Device Manager but displays a warning sign, and the following device status:
Windows has stopped this device because it has reported problems. (Code 43)
The Citrix Hypervisor VM’s /var/log/messages log file contains these error messages:
vmiop_log: error: NVOS status 0x29
vmiop_log: error: Assertion Failed at 0x7620fd4b:179
vmiop_log: error: 8 frames returned by backtrace
...
vmiop_log: error: VGPU message 12 failed, result code: 0x29
...
vmiop_log: error: NVOS status 0x8
vmiop_log: error: Assertion Failed at 0x7620c8df:280
vmiop_log: error: 8 frames returned by backtrace
...
vmiop_log: error: VGPU message 26 failed, result code: 0x8
Resolution
vGPU reserves a portion of the VM’s framebuffer for use in GPU mapping of VM system memory. The reservation is sufficient to support up to 32GB of system memory, and may be increased to accommodate up to 64GB by specifying enable_large_sys_mem=1 in the VM’s platform:vgpu_extra_args parameter:
[root@xenserver ~]# xe vm-param-set uuid=e71afda4-53f4-3a1b-6c92-a364a7f619c2 platform:vgpu_extra_args="enable_large_sys_mem=1"
The setting takes effect the next time the VM is started or rebooted. With this setting in place, less GPU FB is available to applications running in the VM. To accommodate system memory larger than 64GB, the reservation can be further increased by specifying extra_fb_reservation in the VM’s platform:vgpu_extra_args parameter, and setting its value to the desired reservation size in megabytes. The default value of 64M is sufficient to support 64GB of RAM. We recommend adding 2M of reservation for each additional 1GB of system memory. For example, to support 96GB of RAM, set extra_fb_reservation to 128:
platform:vgpu_extra_args="enable_large_sys_mem=1, extra_fb_reservation=128"
The reservation can be reverted back to its default setting in one of the following ways:
- Removing the
vgpu_extra_argskey from theplatformparameter - Removing
enable_large_sys_memfrom thevgpu_extra_argskey - Setting
enable_large_sys_mem=0
3.12. vGPU host driver RPM upgrade fails
Description
Upgrading vGPU host driver RPM fails with an error message about failed dependencies on the console.
[root@xenserver ~]# rpm –U NVIDIA-vGPU-xenserver-6.5-352.46.x86_64.rpm
error: Failed dependencies:
NVIDIA-vgx-xenserver conflicts with NVIDIA-vGPU-xenserver-6.5-352.46.x86_64
[root@xenserver ~]#
Resolution
Uninstall the older vGPU RPM before installing the latest driver.
Use the following command to uninstall the older vGPU RPM:
[root@xenserver ~]# rpm –e NVIDIA-vgx-xenserver
Only resolved issues that have been previously noted as known issues or had a noticeable user impact are listed. The summary and description for each resolved issue indicate the effect of the issue on NVIDIA vGPU software before the issue was resolved.
Issues Resolved in Release 8.10
No resolved issues are reported in this release for Citrix Hypervisor.
Issues Resolved in Release 8.9
No resolved issues are reported in this release for Citrix Hypervisor.
Issues Resolved in Release 8.8
No resolved issues are reported in this release for Citrix Hypervisor.
Issues Resolved in Release 8.7
| Bug ID | Summary and Description |
|---|---|
| 3226853 | 8.0-8.6 Only: NVIDIA vGPU software graphics driver installation fails in Ubuntu guest VMs Installation of the NVIDIA vGPU software graphics driver from a .run file fails in Ubuntu guest VMs that are running Linux kernel version 5.8 or later. |
Issues Resolved in Release 8.6
| Bug ID | Summary and Description |
|---|---|
| 2925629 | 8.0-8.5 Only: Desktop sessions disconnect after the server becomes unresponsive Desktop sessions disconnect after the server becomes unresponsive. Before the sessions disconnect, the error message |
Issues Resolved in Release 8.5
| Bug ID | Summary and Description |
|---|---|
| 200494400 | 8.0-8.4 Only: Citrix Virtual Apps and Desktops connection freezes initially When -0B and -0Q vGPU types are used with Citrix Virtual Apps and Desktops version 7 1903 and later versions, the session freezes or a black screen is seen when the connection is first made. When this issue occurs, the error message |
Issues Resolved in Release 8.4
| Bug ID | Summary and Description |
|---|---|
| 200594274 | When the VMs to which 16 vGPUs on a single GPU (for example 16 T4-1Q vGPUs on a Tesla T4 GPU) are assigned are started simultaneously, only 15 VMs boot and the remaining VM fails to start. When the other VMs are shut down, the VM that failed to start boots successfully. |
| 2814740 | When the hypervisor host is first rebooted after the Virtual GPU Manager is installed, an uncorrectable machine check exception occurs during POST immediately after the message |
| 2870295 | 8.0-8.3 Only: Out of memory errors cause VM crashes on Citrix Hypervisor Out of memory errors caused by extreme memory fragmentation cause VM crashes on Citrix Hypervisor. |
Issues Resolved in Release 8.3
| Bug ID | Summary and Description |
|---|---|
| 2175888 | 8.0-8.2 Only: Even when the scheduling policy is equal share, unequal GPU utilization is reported When the scheduling policy is equal share, unequal GPU engine utilization can be reported for the vGPUs on the same physical GPU. |
Issues Resolved in Release 8.2
| Bug ID | Summary and Description |
|---|---|
| 2644858 | 8.0, 8.1 Only: VMs fail to boot with failed assertions In some scenarios with heavy workloads running on multiple VMs configured with NVIDIA vGPUs on a single pysical GPU, additional VMs configured with NVIDIA vGPU on the same GPU fail to boot. The failure of the VM to boot is followed by failed assertions. This issue affects GPUs based on the NVIDIA Volta GPU architecture and later architectures. |
Issues Resolved in Release 8.1
| Bug ID | Summary and Description |
|---|---|
| 200534988 | Error XID 47 followed by multiple XID 32 errors After disconnecting Citrix Virtual Apps and Desktops and clicking the power button in the VM, error XID 47 occurs followed by multiple XID 32 errors. When these errors occur, the hypervisor host becomes unusable. |
| 200434909 | 8.0 Only: Users' view sessions may become corrupted after migration When a VM configured with vGPU under heavy load is migrated to another host, users' view sessions may become corrupted after the migration. |
| - | 8.0 Only: Incorrect NVIDIA vGPU software Windows graphics driver version in the installer The NVIDIA vGPU software Windows graphics driver version in the installer is incorrect. The driver version incorrectly appears as 325.31 instead of 425.31 in the Extraction path field and the title of the NVIDIA Graphics Driver (325.31) Package Window. |
Issues Resolved in Release 8.0
| Bug ID | Summary and Description |
|---|---|
| 1971698 | NVIDIA vGPU encoder and process utilization counters don't work with Windows Performance Counters GPU encoder and process utilization counter groups are listed in Windows Performance Counters, but no instances of the counters are available. The counters are disabled by default and must be enabled. |
5.1. Restricting Access to GPU Performance Counters
The NVIDIA graphics driver contains a vulnerability (CVE-2018-6260) that may allow access to application data processed on the GPU through a side channel exposed by the GPU performance counters. To address this vulnerability, update the driver and restrict access to GPU performance counters to allow access only by administrator users and users who need to use CUDA profiling tools.
The GPU performance counters that are affected by this vulnerability are the hardware performance monitors used by the CUDA profiling tools such as CUPTI, Nsight Graphics, and Nsight Compute. These performance counters are exposed on the hypervisor host and in guest VMs only as follows:
- On the hypervisor host, they are always exposed. However, the Virtual GPU Manager does not access these performance counters and, therefore, is not affected.
- In Windows and Linux guest VMs, they are exposed only in VMs configured for GPU pass through. They are not exposed in VMs configured for NVIDIA vGPU.
5.1.1. Windows: Restricting Access to GPU Performance Counters for One User by Using NVIDIA Control Panel
Perform this task from the guest VM to which the GPU is passed through.
Ensure that you are running NVIDIA Control Panel version 8.1.950.
- Open NVIDIA Control Panel:
- Right-click on the Windows desktop and select NVIDIA Control Panel from the menu.
- Open Windows Control Panel and double-click the NVIDIA Control Panel icon.
- In NVIDIA Control Panel, select the Manage GPU Performance Counters task in the Developer section of the navigation pane.
- Complete the task by following the instructions in the Manage GPU Performance Counters > Developer topic in the NVIDIA Control Panel help.
5.1.2. Windows: Restricting Access to GPU Performance Counters Across an Enterprise by Using a Registry Key
You can use a registry key to restrict access to GPU Performance Counters for all users who log in to a Windows guest VM. By incorporating the registry key information into a script, you can automate the setting of this registry for all Windows guest VMs across your enterprise.
Perform this task from the guest VM to which the GPU is passed through.
Only enterprise administrators should perform this task. Changes to the Windows registry must be made with care and system instability can result if registry keys are incorrectly set.
- Set the RmProfilingAdminOnly Windows registry key to 1.
[HKLM\SYSTEM\CurrentControlSet\Services\nvlddmkm\Global\NVTweak] Value: "RmProfilingAdminOnly" Type: DWORD Data: 00000001
The data value 1 restricts access, and the data value 0 allows access, to application data processed on the GPU through a side channel exposed by the GPU performance counters.
- Restart the VM.
5.1.3. Linux Guest VMs and Hypervisor Host: Restricting Access to GPU Performance Counters
On systems where unprivileged users don't need to use GPU performance counters, restrict access to these counters to system administrators, namely users with the CAP_SYS_ADMIN capability set. By default, the GPU performance counters are not restricted to users with the CAP_SYS_ADMIN capability.
Perform this task from the guest VM to which the GPU is passed through or from your hypervisor host machine.
In Linux guest VMs, this task requires sudo privileges. On your hypervisor host machine, this task must be performed as the root user on the machine.
- Log in to the guest VM or open a command shell on your hypervisor host machine.
- Set the kernel module parameter NVreg_RestrictProfilingToAdminUsers to 1 by adding this parameter to the /etc/modprobe.d/nvidia.conf file.
-
If you are setting only this parameter, add an entry for it to the /etc/modprobe.d/nvidia.conf file as follows:
options nvidia NVreg_RegistryDwords="NVreg_RestrictProfilingToAdminUsers=1"
-
If you are setting multiple parameters, set them in a single entry as in the following example:
options nvidia NVreg_RegistryDwords="RmPVMRL=0x0" "NVreg_RestrictProfilingToAdminUsers=1"
If the /etc/modprobe.d/nvidia.conf file does not already exist, create it.
-
- Restart the VM or reboot your hypervisor host machine.
6.1. Since 8.9: NVENC does not work with Teradici Cloud Access Software on Windows
Description
The NVIDIA hardware-based H.264/HEVC video encoder (NVENC) does not work with Teradici Cloud Access Software on Windows. This issue affects NVIDIA vGPU and GPU pass through deployments.
This issue occurs because the check that Teradici Cloud Access Software performs on the DLL signer name is case sensitive and NVIDIA recently changed the case of the company name in the signature certificate.
Status
Not an NVIDIA bug
This issue is resolved in the latest 21.07 and 21.03 Teradici Cloud Access Software releases.
Ref. #
200749065
6.2. A licensed client might fail to acquire a license if a proxy is set
Description
If a proxy is set with a system environment variable such as HTTP_PROXY or HTTPS_PROXY, a licensed client might fail to acquire a license.
Workaround
Perform this workaround on each affected licensed client.
-
Add the address of the NVIDIA vGPU software license server to the system environment variable
NO_PROXY.The address must be specified exactly as it is specified in the client's license server settings either as a fully-qualified domain name or an IP address. If the
NO_PROXYenvironment variable contains multiple entries, separate the entries with a comma (,).If high availability is configured for the license server, add the addresses of the primary license server and the secondary license server to the system environment variable
NO_PROXY. -
Restart the NVIDIA driver service that runs the core NVIDIA vGPU software logic.
- On Windows, restart the NVIDIA Display Container service.
- On Linux, restart the nvidia-gridd service.
Status
Closed
Ref. #
200704733
6.3. 8.0-8.6 Only: NVIDIA vGPU software graphics driver installation fails in Ubuntu guest VMs
Description
Installation of the NVIDIA vGPU software graphics driver from a .run file fails in Ubuntu guest VMs that are running Linux kernel version 5.8 or later.
Version
Ubuntu 18.04 LTS with Linux kernel version 5.8 or later
Workaround
Revert to a Linux kernel version earlier than 5.8.
Status
Resolved in NVIDIA vGPU software 8.7
Ref. #
3226853
6.4. 8.0-8.5 Only: Desktop sessions disconnect after the server becomes unresponsive
Description
Desktop sessions disconnect after the server becomes unresponsive. Before the sessions disconnect, the error message VGPU message 32 failed, result code: 0x59 is written to the log files on the hypervisor host.
Status
Resolved in NVIDIA vGPU software 8.6
Ref. #
2925629
6.5. 8.0-8.3 Only: When the VMs to which 16 vGPUs on a single GPU are assigned are started simultaneously, one VM fails to boot
Description
When the VMs to which 16 vGPUs on a single GPU (for example 16 T4-1Q vGPUs on a Tesla T4 GPU) are assigned are started simultaneously, only 15 VMs boot and the remaining VM fails to start. When the other VMs are shut down, the VM that failed to start boots successfully.
The log file on the hypervisor host contains these error messages:
2020-03-04T16:01:13.626Z| vmx| E110: vmiop_log: NVOS status 0x51
2020-03-04T16:01:13.626Z| vmx| E110: vmiop_log: Assertion Failed at 0x5e530d8c:303
...
2020-03-04T16:01:13.626Z| vmx| E110: vmiop_log: (0x0): Failed to alloc guest FB memory
2020-03-04T16:01:13.626Z| vmx| E110: vmiop_log: (0x0): init_device_instance failed for inst 0 with error 2 (vmiop-display: error allocating framebuffer)
2020-03-04T16:01:13.626Z| vmx| E110: vmiop_log: (0x0): Initialization: init_device_instance failed error 2
2020-03-04T16:01:13.629Z| vmx| E110: vmiop_log: display_init failed for inst: 0
Status
Resolved in NVIDIA vGPU software 8.4
Ref. #
200594274
6.6. 8.0, 8.1 Only: VMs fail to boot with failed assertions
Description
In some scenarios with heavy workloads running on multiple VMs configured with NVIDIA vGPUs on a single pysical GPU, additional VMs configured with NVIDIA vGPU on the same GPU fail to boot. The failure of the VM to boot is followed by failed assertions. This issue affects GPUs based on the NVIDIA Volta GPU architecture and later architectures.
When this error occurs, error messages similar to the following examples are logged to the Citrix Hypervisor log file/var/log/messages:
nvidia-vgpu-mgr[31526]: error: vmiop_log: NVOS status 0x1e
nvidia-vgpu-mgr[31526]: error: vmiop_log: Assertion Failed at 0xb2d3e4d7:96
nvidia-vgpu-mgr[31526]: error: vmiop_log: 12 frames returned by backtrace
nvidia-vgpu-mgr[31526]: error: vmiop_log: /usr/lib64/libnvidia-vgpu.so(_nv003956vgpu+0x18) [0x7f4bb2cfb338] vmiop_dump_stack
nvidia-vgpu-mgr[31526]: error: vmiop_log: /usr/lib64/libnvidia-vgpu.so(_nv004018vgpu+0xd4) [0x7f4bb2d09ce4] vmiopd_alloc_pb_channel
nvidia-vgpu-mgr[31526]: error: vmiop_log: /usr/lib64/libnvidia-vgpu.so(_nv002878vgpu+0x137) [0x7f4bb2d3e4d7] vgpufceInitCopyEngine_GK104
nvidia-vgpu-mgr[31526]: error: vmiop_log: /usr/lib64/libnvidia-vgpu.so(+0x80e27) [0x7f4bb2cd0e27]
nvidia-vgpu-mgr[31526]: error: vmiop_log: /usr/lib64/libnvidia-vgpu.so(+0x816a7) [0x7f4bb2cd16a7]
nvidia-vgpu-mgr[31526]: error: vmiop_log: vgpu() [0x413820]
nvidia-vgpu-mgr[31526]: error: vmiop_log: vgpu() [0x413a8d]
nvidia-vgpu-mgr[31526]: error: vmiop_log: vgpu() [0x40e11f]
nvidia-vgpu-mgr[31526]: error: vmiop_log: vgpu() [0x40bb69]
nvidia-vgpu-mgr[31526]: error: vmiop_log: vgpu() [0x40b51c]
nvidia-vgpu-mgr[31526]: error: vmiop_log: /lib64/libc.so.6(__libc_start_main+0x100) [0x7f4bb2feed20]
nvidia-vgpu-mgr[31526]: error: vmiop_log: vgpu() [0x4033ea]
nvidia-vgpu-mgr[31526]: error: vmiop_log: (0x0): Alloc Channel(Gpfifo) for device failed error: 0x1e
nvidia-vgpu-mgr[31526]: error: vmiop_log: (0x0): Failed to allocate FCE channel
nvidia-vgpu-mgr[31526]: error: vmiop_log: (0x0): init_device_instance failed for inst 0 with error 2 (init frame copy engine)
nvidia-vgpu-mgr[31526]: error: vmiop_log: (0x0): Initialization: init_device_instance failed error 2
nvidia-vgpu-mgr[31526]: error: vmiop_log: display_init failed for inst: 0
nvidia-vgpu-mgr[31526]: error: vmiop_env_log: (0x0): vmiope_process_configuration: plugin registration error
nvidia-vgpu-mgr[31526]: error: vmiop_env_log: (0x0): vmiope_process_configuration failed with 0x1a
kernel: [858113.083773] [nvidia-vgpu-vfio] ace3f3bb-17d8-4587-920e-199b8fed532d: start failed. status: 0x1
Status
Resolved in NVIDIA vGPU software 8.2
Ref. #
2644858
6.7. NVIDIA Control Panel fails to start if launched too soon from a VM without licensing information
Description
If NVIDIA licensing information is not configured on the system, any attempt to start NVIDIA Control Panel by right-clicking on the desktop within 30 seconds of the VM being started fails.
Workaround
Wait at least 30 seconds before trying to launch NVIDIA Control Panel.
Status
Open
Ref. #
200623179
6.8. DWM crashes randomly occur in Windows VMs
Description
Desktop Windows Manager (DWM) crashes randomly occur in Windows VMs, causing a blue-screen crash and the bug check CRITICAL_PROCESS_DIED. Computer Management shows problems with the primary display device.
Version
This issue affects Windows 10 1809, 1903 and 1909 VMs.
Status
Not an NVIDIA bug
Ref. #
2730037
6.9. 8.0-8.4 Only: Citrix Virtual Apps and Desktops connection freezes initially
Description
When -0B and -0Q vGPU types are used with Citrix Virtual Apps and Desktops version 7 1903 and later versions, the session freezes or a black screen is seen when the connection is first made. When this issue occurs, the error message DXGI_ERROR_DEVICE_REMOVED is displayed. The affected versions of Citrix Virtual Apps and Desktops use Microsoft DDAPI.
Version
Citrix Virtual Apps and Desktops version 7 1903 and later versions
Workaround
Disable the use hardware encoding for video codec Citrix policy, which is enabled by default.
Status
Resolved in NVIDIA vGPU software 8.5
Ref. #
200494400
6.10. 8.0-8.3 Only: Uncorrectable machine check exception occurs after initial reboot of the hypervisor host
Description
When the hypervisor host is first rebooted after the Virtual GPU Manager is installed, an uncorrectable machine check exception occurs during POST immediately after the message SYSTEM CHIPSET INITIALIZATION UPI LINK INITIALIZATION - START. This issue affects HP systems that are running a hypervisor release that has a newer kernel, for example, Citrix Hypervisor 8.0 or 8.1.
After the uncorrectable machine check exception, the hypervisor host is automatically reset and returns to a working state.
When this issue occurs, the following error messages are logged:
Uncorrectable Machine Check Exception (Processor 1, APIC ID 0x00000000, Bank 0x00000006,
Status 0xFB800000'00000E0B, Address 0x00000000'00000000, Misc 0x00000000'5B000000).
Uncorrectable PCI Express Error Detected. Slot 255 (Segment 0x0, Bus 0x5D, Device 0x48, Function 0x0)
Uncorrectable PCI Express Error Detected. Slot 255 (Segment 0x0, Bus 0x5D, Device 0x88, Function 0x0)
Uncorrectable PCI Express Error Detected. Slot 255 (Segment 0x0, Bus 0x5D, Device 0x80, Function 0x0)
Uncorrectable PCI Express Error Detected. Slot 255 (Segment 0x0, Bus 0x5D, Device 0x40, Function 0x0)
Workaround
Wait for the host to return to a working state. No other action is required.
Status
Resolved in NVIDIA vGPU software 8.4
Ref. #
2814740
6.11. 8.0-8.3 Only: Out of memory errors cause VM crashes on Citrix Hypervisor
Description
Out of memory errors caused by extreme memory fragmentation cause VM crashes on Citrix Hypervisor.
When this issue occurs, error messages similar to the following examples are logged:
Feb 4 10:45:53 copic-xs-4 kernel: [3067294.076077] Out of memory: Kill process 6989 (xapi) score 7 or sacrifice child
Feb 4 10:45:53 copic-xs-4 kernel: [3067294.076399] Killed process 6989 (xapi) total-vm:638288kB, anon-rss:53824kB, file-rss:9292kB, shmem-rss:4kB
Feb 4 10:45:53 copic-xs-4 kernel: [3067294.138425] oom_reaper: reaped process 6989 (xapi), now anon-rss:0kB, file-rss:8kB, shmem-rss:4kB
The kill process in the messages might be different than xapi.
Workaround
Increase the memory for the Citrix Hypervisor dom0 domain to at least 16 GB.
Status
Resolved in NVIDIA vGPU software 8.4
Ref. #
2870295
6.12. NVIDIA Control Panel fails to launch in a platform layer or published image
Description
When NVIDIA vGPU software is used with Citrix App Layering and a platform layer for a vGPU is being configured, NVIDIA Control Panel might fail to launch. The driver might be working normally or it might fail with code 31 or code 43.
For more information and a workaround for this issue, see NVDIA Control Panel fails to launch in platform layer or published image in the Citrix Support Knowledge Center.
6.13. Citrix Virtual Apps and Desktops session freezes when the desktop is unlocked
Description
When a Citrix Virtual Apps and Desktops session that is locked is unlocked by pressing Ctrl+Alt+Del, the session freezes. This issue affects only VMs that are running Microsoft Windows 10 1809 as a guest OS.
Version
Microsoft Windows 10 1809 guest OS
Workaround
Restart the VM.
Status
Not an NVIDIA bug
Ref. #
2767012
6.14. NVIDIA vGPU software graphics driver fails after Linux kernel upgrade with DKMS enabled
Description
After the Linux kernel is upgraded (for example by running sudo apt full-upgrade) with Dynamic Kernel Module Support (DKMS) enabled, the nvidia-smi command fails to run. If DKMS is enabled, an upgrade to the Linux kernel triggers a rebuild of the NVIDIA vGPU software graphics driver. The rebuild of the driver fails because the compiler version is incorrect. Any attempt to reinstall the driver fails because the kernel fails to build.
When the failure occurs, the following messages are displayed:
-> Installing DKMS kernel module:
ERROR: Failed to run `/usr/sbin/dkms build -m nvidia -v 418.70 -k 5.3.0-28-generic`:
Kernel preparation unnecessary for this kernel. Skipping...
Building module:
cleaning build area...
'make' -j8 NV_EXCLUDE_BUILD_MODULES='' KERNEL_UNAME=5.3.0-28-generic IGNORE_CC_MISMATCH='' modules...(bad exit status: 2)
ERROR (dkms apport): binary package for nvidia: 418.70 not found
Error! Bad return status for module build on kernel: 5.3.0-28-generic (x86_64)
Consult /var/lib/dkms/nvidia/ 418.70/build/make.log for more information.
-> error.
ERROR: Failed to install the kernel module through DKMS. No kernel module was installed;
please try installing again without DKMS, or check the DKMS logs for more information.
ERROR: Installation has failed. Please see the file '/var/log/nvidia-installer.log' for details.
You may find suggestions on fixing installation problems in the README available on the Linux driver download page at www.nvidia.com.
Workaround
When installing the NVIDIA vGPU software graphics driver with DKMS enabled, use one of the following workarounds:
- Before running the driver installer, install the
dkmspackage, then run the driver installer with the -dkms option. - Run the driver installer with the --no-cc-version-check option.
Status
Not a bug.
Ref. #
2836271
6.15. A PCIe bus error occurs in iLO after Tesla M10 installation
Description
When a Tesla M10 GPU is installed in an HPE ProLiant DL380 Gen9 or Gen10 server that is running Citrix Hypervisor 8.0, a PCIe bus error occurs in the Integrated Lights-Out (iLO) remote server management processor. When this error occurs, the server can no longer be shut down, the error message CPU Panic is issued, and a reboot of the server is forced.
This issue is specific to the PLX chip on the Tesla M10 GPU.
Version
This issue affects only the following combination of software and hardware:
- Hypervisor software: Citrix Hypervisor 8.0
- Server hardware: HPE ProLiant DL380 Gen9 or Gen10
- GPU hardware: Tesla M10
Status
Open
Ref. #
200588187
6.16. 8.0 Only: Users' view sessions may become corrupted after migration
Description
When a VM configured with vGPU under heavy load is migrated to another host, users' view sessions may become corrupted after the migration.
Workaround
Restart the VM.
Status
Resolved in NVIDIA vGPU software release 8.1.
Ref. #
200434909
6.17. Migrating a VM configured with NVIDIA vGPU software release 8.1 to a host running release 8.0 fails
Description
If a VM configured with NVIDIA vGPU software release 8.1 is migrated to a host running NVIDIA vGPU software release 8.0, the migration fails and the VM shuts down.
This issue occurs only with the following combination of releases of guest VM graphics driver, vGPU manager on the source host, and vGPU manager on the destination host:
| Guest VM Graphics Driver | Source vGPU Manager | Destination vGPU Manager |
|---|---|---|
| 8.1 | 8.1 | 8.0 |
Workaround
- On the host that is running vGPU Manager 8.1, set the registry key
RMSetVGPUVersionMaxto 0x20001. - Start the VM.
- Confirm that the vGPU version in the log files is 0x20001.
2019-07-09T10:19:05.420Z| vthread-2142280| I125: vmiop_log: vGPU version: 0x20001
The VM can now be migrated.
Status
Open
Ref. #
200533827
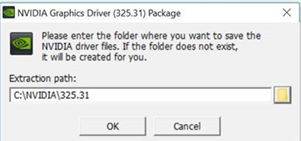
6.18. 8.0 Only: Incorrect NVIDIA vGPU software Windows graphics driver version in the installer
Description
The NVIDIA vGPU software Windows graphics driver version in the installer is incorrect. The driver version incorrectly appears as 325.31 instead of 425.31 in the Extraction path field and the title of the NVIDIA Graphics Driver (325.31) Package Window.
Version
NVIDIA vGPU software Windows graphics driver version 425.31 in NVIDIA vGPU software release 8.0
Workaround
To simplify future administration of your system, you can correct the driver version in the folder name when the installer prompts you for the extraction path. However, if you do not change the name of the folder in the extraction path, the installation succeeds and the driver functions correctly.
Status
Resolved in NVIDIA vGPU software release 8.1
6.19. Incorrect GPU type shown for Quadro RTX 8000 GPUs in Citrix XenCenter
Description
On the GPU tab in Citrix XenCenter, Quadro RTX 8000 GPUs are incorrectly shown as [QUADRO RTX 6000].
However, the virtual GPU types for a Quadro RTX 8000 GPU are listed correctly.
NVIDIA vGPU software does not support systems with a mixture of GPU types. Therefore, you can assume that any GPU in a system that you know to contain Quadro RTX 8000 GPUs that is shown as [QUADRO RTX 6000] is, in fact, a Quadro RTX 8000 GPU.
Status
Not an NVIDIA bug
Ref. #
200492607
6.20. NVIDIA Notification Icon prevents log off of Citrix Published Application user sessions
Description
By default on Windows Server operating systems, the NVIDIA Notification Icon application is started with every Citrix Published Application user session. This application might prevent the Citrix Published Application user session from being logged off even after the user has quit all other applications.
Resolution
Disable the NVIDIA Notification Icon application for Citrix Published Application user sessions as explained in Virtual GPU Software User Guide.
Status
Resolved by the provision of Windows registry keys for disabling the NVIDIA Notification Icon application for Citrix Published Application user sessions.
Ref. #
2206368
6.21. Vulkan applications crash in Windows 7 guest VMs configured with NVIDIA vGPU
Description
In Windows 7 guest VMs configured with NVIDIA vGPU, applications developed with Vulkan APIs crash or throw errors when they are launched. Vulkan APIs require sparse texture support, but in Windows 7 guest VMs configured with NVIDIA vGPU, sparse textures are not enabled.
In Windows 10 guest VMs configured with NVIDIA vGPU, sparse textures are enabled and applications developed with Vulkan APIs run correctly in these VMs.
Status
Open
Ref. #
200381348
6.22. Host core CPU utilization is higher than expected for moderate workloads
Description
When GPU performance is being monitored, host core CPU utilization is higher than expected for moderate workloads. For example, host CPU utilization when only a small number of VMs are running is as high as when several times as many VMs are running.
Workaround
Disable monitoring of the following GPU performance statistics:
- vGPU engine usage by applications across multiple vGPUs
- Encoder session statistics
- Frame buffer capture (FBC) session statistics
- Statistics gathered by performance counters in guest VMs
Status
Open
Ref. #
2414897
6.23. Frame capture while the interactive logon message is displayed returns blank screen
Description
Because of a known limitation with NvFBC, a frame capture while the interactive logon message is displayed returns a blank screen.
An NvFBC session can capture screen updates that occur after the session is created. Before the logon message appears, there is no screen update after the message is shown and, therefore, a black screen is returned instead. If the NvFBC session is created after this update has occurred, NvFBC cannot get a frame to capture.
Workaround
See Black Screen at Logon with Nvidia HDX 3D Pro enabled in the Citrix knowledge base.
Status
Not a bug
Ref. #
2115733
6.24. RDS sessions do not use the GPU with some Microsoft Windows Server releases
Description
When some releases of Windows Server are used as a guest OS, Remote Desktop Services (RDS) sessions do not use the GPU. With these releases, the RDS sessions by default use the Microsoft Basic Render Driver instead of the GPU. This default setting enables 2D DirectX applications such as Microsoft Office to use software rendering, which can be more efficient than using the GPU for rendering. However, as a result, 3D applications that use DirectX are prevented from using the GPU.
Version
- Windows Server 2019
- Windows Server 2016
- Windows Server 2012
Solution
Change the local computer policy to use the hardware graphics adapter for all RDS sessions.
-
Choose Local Computer Policy > Computer Configuration > Administrative Templates > Windows Components > Remote Desktop Services > Remote Desktop Session Host > Remote Session Environment.
-
Set the Use the hardware default graphics adapter for all Remote Desktop Services sessions option.
6.25. Cloned VMs configured with a vGPU type different than the type in the master image fail to start
Description
Cloned VMs configured with a vGPU type different than the type in the master image fail to start.
When a Windows 10 VM is booted, the VM becomes stuck in a loop and alternately displays Getting devices ready: 50% and Preparation in progress.
Workaround
Create one master image for each vGPU type that you want to use. Do not attempt to configure a cloned VM with a vGPU type different than the type in the master image.
Status
Not an NVIDIA bug
Ref. #
2285306
6.26. 8.0-8.2 Only: Even when the scheduling policy is equal share, unequal GPU utilization is reported
Description
When the scheduling policy is equal share, unequal GPU engine utilization can be reported for the vGPUs on the same physical GPU.
For example, GPU engine usage for three P40-8Q vGPUs on a Tesla P40 GPU might be reported as follows:
[root@localhost:~] nvidia-smi vgpu
Wed Jun 27 10:33:18 2018
+-----------------------------------------------------------------------------+
| NVIDIA-SMI 390.59 Driver Version: 390.59 |
|-------------------------------+--------------------------------+------------+
| GPU Name | Bus-Id | GPU-Util |
| vGPU ID Name | VM ID VM Name | vGPU-Util |
|===============================+================================+============|
| 0 Tesla P40 | 00000000:81:00.0 | 52% |
| 2122661 GRID P40-8Q | 2122682 centos7.4-xmpl-211... | 19% |
| 2122663 GRID P40-8Q | 2122692 centos7.4-xmpl-211... | 0% |
| 2122659 GRID P40-8Q | 2122664 centos7.4-xmpl-211... | 25% |
+-------------------------------+--------------------------------+------------+
| 1 Tesla P40 | 00000000:85:00.0 | 58% |
| 2122662 GRID P40-8Q | 2122689 centos7.4-xmpl-211... | 0% |
| 2122658 GRID P40-8Q | 2122667 centos7.4-xmpl-211... | 59% |
| 2122660 GRID P40-8Q | 2122670 centos7.4-xmpl-211... | 0% |
+-------------------------------+--------------------------------+------------+
The vGPU utilization of the vGPU 2122658 is reported as 59%. However, the expected vGPU utilization should not exceed 33%.
This behavior is a result of the mechanism that is used to measure GPU engine utilization.
Status
Resolved in NVIDIA vGPU software 8.3
Ref. #
2175888
6.27. When the scheduling policy is fixed share, GPU utilization is reported as higher than expected
Description
When the scheduling policy is fixed share, GPU engine utilization can be reported as higher than expected for a vGPU.
For example, GPU engine usage for six P40-4Q vGPUs on a Tesla P40 GPU might be reported as follows:
[root@localhost:~] nvidia-smi vgpu
Mon Aug 20 10:33:18 2018
+-----------------------------------------------------------------------------+
| NVIDIA-SMI 390.42 Driver Version: 390.42 |
|-------------------------------+--------------------------------+------------+
| GPU Name | Bus-Id | GPU-Util |
| vGPU ID Name | VM ID VM Name | vGPU-Util |
|===============================+================================+============|
| 0 Tesla P40 | 00000000:81:00.0 | 99% |
| 85109 GRID P40-4Q | 85110 win7-xmpl-146048-1 | 32% |
| 87195 GRID P40-4Q | 87196 win7-xmpl-146048-2 | 39% |
| 88095 GRID P40-4Q | 88096 win7-xmpl-146048-3 | 26% |
| 89170 GRID P40-4Q | 89171 win7-xmpl-146048-4 | 0% |
| 90475 GRID P40-4Q | 90476 win7-xmpl-146048-5 | 0% |
| 93363 GRID P40-4Q | 93364 win7-xmpl-146048-6 | 0% |
+-------------------------------+--------------------------------+------------+
| 1 Tesla P40 | 00000000:85:00.0 | 0% |
+-------------------------------+--------------------------------+------------+
The vGPU utilization of vGPU 85109 is reported as 32%. For vGPU 87195, vGPU utilization is reported as 39%. And for 88095, it is reported as 26%. However, the expected vGPU utilization of any vGPU should not exceed approximately 16.7%.
This behavior is a result of the mechanism that is used to measure GPU engine utilization.
Status
Open
Ref. #
2227591
6.28. nvidia-smi reports that vGPU migration is supported on all hypervisors
Description
The command nvidia-smi vgpu -m shows that vGPU migration is supported on all hypervisors, even hypervisors or hypervisor versions that do not support vGPU migration.
Status
Closed
Ref. #
200407230
6.29. NVIDIA Control Panel Crashes in a VM connected to two 4K displays
Description
When NVIDIA Control Panel is started in a VM connected through a pass-through GPU to two 4K displays, a Citrix HDX 3D Pro Warning pop-up window opens containing the following error message:
Full screen applications are not supported on Citrix HDX 3D Pro. Press Ok to exit
NVIDIA Control Panel then crashes.
After the VM is rebooted, NVIDIA Control Panel is available again.
Version
Citrix Virtual Apps and Desktops 7.16
Status
Not an NVIDIA bug
Ref. #
200393766
6.30. vGPU guest VM driver not properly loaded on servers with more than 512 GB or 1 TB or more of system memory
Description
If PV IOMMU is enabled, support for vGPU is limited to servers with a maximum of 512 GB of system memory. On servers with more than 512 GB of system memory and PV IOMMU enabled, the guest VM driver is not properly loaded. Device Manager marks the vGPU with a yellow exclamation point.
If PV IOMMU is disabled, support for vGPU is limited to servers with less than 1 TB of system memory. This limitation applies only to systems with supported GPUs based on the Maxwell architecture: Tesla M6, Tesla M10, and Tesla M60. On servers with 1 TB or more of system memory, VMs configured with vGPU fail to power on. However, support for GPU pass through is not affected by this limitation.
Resolution
-
If PV IOMMU is enabled, disable it.
[root@xenserver ~]# /opt/xensource/libexec/xen-cmdline --set-xen iommu=dom0-passthrough
-
If the server has 1 TB or more of system memory, limit the amount of system memory on the server to 1 TB minus 16 GB.
If the server has less than 1 TB or more of system memory, omit this step.
-
Reboot the server.
Status
Not an NVIDIA bug
Ref. #
1799582
6.31. Luxmark causes a segmentation fault on an unlicensed Linux client
Description
If the Luxmark application is run on a Linux guest VM configured with NVIDIA vGPU that is booted without acquiring a license, a segmentation fault occurs and the application core dumps. The fault occurs when the application cannot allocate a CUDA object on NVIDIA vGPUs where CUDA is disabled. On NVIDIA vGPUs that can support CUDA, CUDA is disabled in unlicensed mode.
Status
Not an NVIDIA bug.
Ref. #
200330956
6.32. Resolution is not updated after a VM acquires a license and is restarted
Description
In a Red Enterprise Linux 7.3 guest VM, an increase in resolution from 1024×768 to 2560×1600 is not applied after a license is acquired and the gridd service is restarted. This issue occurs if the multimonitor parameter is added to the xorg.conf file.
Version
Red Enterprise Linux 7.3
Status
Open
Ref. #
200275925
6.33. On Tesla P40, P6, and P4 GPUs, the default ECC setting prevents NVIDIA vGPU from starting
Description
On Tesla P40, Tesla P6, and Tesla P4 GPUs, the default error-correcting code (ECC) memory setting prevents NVIDIA vGPU from starting. By default, ECC memory is enabled on these GPUs, but NVIDIA vGPU does not support ECC memory.
Workaround
Before running NVIDIA vGPU, disable ECC memory as explained in Virtual GPU Software User Guide.
Status
Closed.
Ref. #
200269717
6.34. A segmentation fault in DBus code causes
nvidia-gridd
to exit on Red Hat Enterprise Linux and CentOS
Description
On Red Hat Enterprise Linux 6.8 and 6.9, and CentOS 6.8 and 6.9, a segmentation fault in DBus code causes the nvidia-gridd service to exit.
The nvidia-gridd service uses DBus for communication with NVIDIA X Server Settings to display licensing information through the Manage License page. Disabling the GUI for licensing resolves this issue.
To prevent this issue, the GUI for licensing is disabled by default. You might encounter this issue if you have enabled the GUI for licensing and are using Red Hat Enterprise Linux 6.8 or 6.9, or CentOS 6.8 and 6.9.
Version
Red Hat Enterprise Linux 6.8 and 6.9
CentOS 6.8 and 6.9
Status
Open
Ref. #
- 200358191
- 200319854
- 1895945
6.35. No Manage License option available in NVIDIA X Server Settings by default
Description
By default, the Manage License option is not available in NVIDIA X Server Settings. This option is missing because the GUI for licensing on Linux is disabled by default to work around the issue that is described in A segmentation fault in DBus code causes nvidia-gridd to exit on Red Hat Enterprise Linux and CentOS.
Workaround
This workaround requires sudo privileges.
Do not use this workaround with Red Hat Enterprise Linux 6.8 and 6.9 or CentOS 6.8 and 6.9. To prevent a segmentation fault in DBus code from causing the nvidia-gridd service from exiting, the GUI for licensing must be disabled with these OS versions.
- If NVIDIA X Server Settings is running, shut it down.
-
If the /etc/nvidia/gridd.conf file does not already exist, create it by copying the supplied template file /etc/nvidia/gridd.conf.template.
-
As root, edit the /etc/nvidia/gridd.conf file to set the
EnableUIoption toTRUE. -
Start the
nvidia-griddservice.# sudo service nvidia-gridd start
When NVIDIA X Server Settings is restarted, the Manage License option is now available.
Status
Open
6.36. Licenses remain checked out when VMs are forcibly powered off
Description
NVIDIA vGPU software licenses remain checked out on the license server when non-persistent VMs are forcibly powered off.
The NVIDIA service running in a VM returns checked out licenses when the VM is shut down. In environments where non-persistent licensed VMs are not cleanly shut down, licenses on the license server can become exhausted. For example, this issue can occur in automated test environments where VMs are frequently changing and are not guaranteed to be cleanly shut down. The licenses from such VMs remain checked out against their MAC address for seven days before they time out and become available to other VMs.
Resolution
If VMs are routinely being powered off without clean shutdown in your environment, you can avoid this issue by shortening the license borrow period. To shorten the license borrow period, set the LicenseInterval configuration setting in your VM image. For details, refer to Virtual GPU Client Licensing User Guide.
Status
Closed
Ref. #
1694975
6.37. Memory exhaustion can occur with vGPU profiles that have 512 Mbytes or less of frame buffer
Description
Memory exhaustion can occur with vGPU profiles that have 512 Mbytes or less of frame buffer.
This issue typically occurs in the following situations:
- Full screen 1080p video content is playing in a browser. In this situation, the session hangs and session reconnection fails.
- Multiple display heads are used with Citrix Virtual Apps and Desktops or VMware Horizon on a Windows 10 guest VM.
- Higher resolution monitors are used.
- Applications that are frame-buffer intensive are used.
- NVENC is in use.
To reduce the possibility of memory exhaustion, NVENC is disabled on profiles that have 512 Mbytes or less of frame buffer.
When memory exhaustion occurs, the NVIDIA host driver reports Xid error 31 and Xid error 43 in the Citrix Hypervisor/var/log/messages file.
The following vGPU profiles have 512 Mbytes or less of frame buffer:
- Tesla M6-0B, M6-0Q
- Tesla M10-0B, M10-0Q
- Tesla M60-0B, M60-0Q
The root cause is a known issue associated with changes to the way that recent Microsoft operating systems handle and allow access to overprovisioning messages and errors. If your systems are provisioned with enough frame buffer to support your use cases, you should not encounter these issues.
Workaround
- Use an appropriately sized vGPU to ensure that the frame buffer supplied to a VM through the vGPU is adequate for your workloads.
- Monitor your frame buffer usage.
- If you are using Windows 10, consider these workarounds and solutions:
-
Use a profile that has 1 Gbyte of frame buffer.
-
Optimize your Windows 10 resource usage.
To obtain information about best practices for improved user experience using Windows 10 in virtual environments, complete the NVIDIA GRID vGPU Profile Sizing Guide for Windows 10 download request form.
For more information, see also Windows 10 Optimization for XenDesktop on the Citrix blog.
-
Status
Open
Ref. #
- 200130864
- 1803861
6.38. VM bug checks after the guest VM driver for Windows 10 RS2 is installed
Description
When the VM is rebooted after the guest VM driver for Windows 10 RS2 is installed, the VM bug checks. When Windows boots, it selects one of the standard supported video modes. If Windows is booted directly with a display that is driven by an NVIDIA driver, for example a vGPU on Citrix Hypervisor, a blue screen crash occurs.
This issue occurs when the screen resolution is switched from VGA mode to a resolution that is higher than 1920×1200.
Fix
Download and install Microsoft Windows Update KB4020102 from the Microsoft Update Catalog.
Workaround
If you have applied the fix, ignore this workaround.
Otherwise, you can work around this issue until you are able to apply the fix by not using resolutions higher than 1920×1200.
- Choose a GPU profile in Citrix XenCenter that does not allow resolutions higher than 1920×1200.
- Before rebooting the VM, set the display resolution to 1920×1200 or lower.
Status
Not an NVIDIA bug
Ref. #
200310861
6.39. On Citrix Hypervisor 7.0, VMs unexpectedly reboot and Citrix Hypervisor crashes or freezes
Description
On Citrix Hypervisor 7.0, VMs to which a vGPU is attached unexpectedly reboot and Citrix Hypervisor crashes or freezes.
The event log in the Citrix Hypervisor/var/log/crash/xen.log file lists the following errors:
- A fatal bus error on a component at the slot where the GPU card is installed
- A fatal error on a component at bus 0, device 2, function 0
This issue occurs when page-modification logging (PML) is enabled on Intel Broadwell CPUs running Citrix Hypervisor 7.0. Citrix is aware of this issue and is working on a permanent fix.
Workaround
Disable page-modification logging (PML) as explained in XenServer 7 host crash while starting multiple virtual machines in the Citrix Support Knowledge Center.
Status
Not an NVIDIA bug
Ref. #
1853248
6.40. With no NVIDIA driver installed, Citrix Hypervisor misidentifies Tesla M10 cards
Description
An erroneous entry in the pci.ids database causes Citrix Hypervisor to identify Tesla M10 cards as GRID M40 when no NVIDIA driver is installed.
Version
Citrix Hypervisor 6.5 and 7.0
Workaround
None
Status
Not an NVIDIA bug
Ref. #
NVIDIA-420/1792341
6.41. GNOME Display Manager (GDM) fails to start on Red Hat Enterprise Linux 7.2 and CentOS 7.0
Description
GDM fails to start on Red Hat Enterprise Linux 7.2 and CentOS 7.0 with the following error:
Oh no! Something has gone wrong!
Workaround
Permanently enable permissive mode for Security Enhanced Linux (SELinux).
- As root, edit the /etc/selinux/config file to set
SELINUXtopermissive.SELINUX=permissive
- Reboot the system.
~]# reboot
For more information, see Permissive Mode in Red Hat Enterprise Linux 7 SELinux User's and Administrator's Guide.
Status
Not an NVIDIA bug
Ref. #
200167868
6.42. Video goes blank when run in loop in Windows Media Player
Description
When connected to a vGPU-enabled VM using Citrix Virtual Apps and Desktops, a video played back in looping mode on Windows Media Player goes blank or freezes after a few iterations.
Workaround
None
Status
Not an NVIDIA bug
Ref. #
1306623
6.43. Local VGA console is momentarily unblanked when Citrix Virtual Apps and Desktops changes resolution of the VM desktop
Description
When Citrix Virtual Apps and Desktops establishes a remote connection to a VM using vGPU, the VM’s local VGA console display in XenCenter is blanked (assuming the VM local console has not been disabled by setting platform:vgpu_extra_args="disable_vnc=1"). If the Citrix Virtual Apps and Desktops session changes resolution of the VM’s desktop, the local VGA console momentarily unblanks, allowing a XenCenter user to briefly view the desktop.
Workaround
Disable the VM’s local VGA console
xe vm-param-set uuid=vm-uuid platform:vgpu_extra_args="disable_vnc=1"
Status
Open
Ref. #
NVIDIA-145/1375164
6.44. VM bugchecks on shutdown/restart when Citrix Virtual Apps and Desktops is installed and NVIDIA driver is uninstalled or upgraded.
Description
If the Citrix Virtual Apps and Desktops agent is installed in a VM before any NVIDIA GPU driver is installed, the VM will bugcheck (bluescreen) when the NVIDIA driver is subsequently upgraded or uninstalled. The bugcheck code is 0x7E, SYSTEM_THREAD_EXCEPTION_NOT_HANDLED.
Workaround
Use one of the following workarounds:
- Do a force shutdown of the VM and restart it.
- Install the NVIDIA driver in guest VMs before installing Citrix Virtual Apps and Desktops.
Status
Open
Ref. #
NVIDIA-295/200018125
6.45. Application frame rate may drop when running Citrix Virtual Apps and Desktops at 2560×1600 resolution.
Description
An application’s rendering frame rate may drop when running Citrix Virtual Apps and Desktops at 2560×1600 resolution, relative to the frame rate obtained at lower resolutions.
Fix
Using the Windows regedit utility within the VM, open the HKLM\SOFTWARE\Citrix\Graphics registry key and create a new DWORD value, EncodeSpeed, with a value of 2. Reboot the VM. This setting may improve the delivered frame rate at the expense of a reduction in image quality.
Status
Open
Ref. #
NVIDIA-190/1416336
6.46. Windows VM BSOD
Description
Windows VM bugchecks on Citrix Hypervisor when running a large number of vGPU based VMs.
The Citrix Hypervisor/var/log/messages file contains these error messages:
NVRM: Xid (PCI:0000:08:00): 31, Ch 0000001e, engmask 00000111, intr 10000000
NVRM: Xid (PCI:0000:08:00): 31, Ch 00000016, engmask 00000111, intr 10000000
...
vmiop_log: error: Assertion Failed at 0xb5b898d8:4184
vmiop_log: error: 8 frames returned by backtrace
vmiop_log: error: /usr/lib/libnvidia-vgx.so(_nv000793vgx+0x69d) [0xb5b8064d]
vmiop_log: error: /usr/lib/libnvidia-vgx.so(_nv000479vgx+0x118) [0xb5b898d8]
vmiop_log: error: /usr/lib/libnvidia-vgx.so(_nv000782vgx+0x59) [0xb5b85f49]
vmiop_log: error: /usr/lib/libnvidia-vgx.so(_nv000347vgx+0x3db) [0xb5b932db]
vmiop_log: error: /usr/lib/libnvidia-vgx.so [0xb5b78e4a]
vmiop_log: error: /usr/lib/xen/bin/vgpu [0x80554be]
vmiop_log: error: /lib/libpthread.so.0 [0xb7612912]
vmiop_log: error: /lib/libc.so.6(clone+0x5e) [0xb76fc5ee]
vmiop_log: error: failed to initialize guest PTE entries
vmiop_log: error: failed to fill up guest PTE entries 3
vmiop_log: error: VGPU message 27 failed, result code: 0xff000003
vmiop_log: error: 0xc1d00001, 0xff010000, 0x1a77ba000, 0x0, 0x1,
vmiop_log: error: 0x1, 0x1000, 0x10202, 0xc1d00001, 0xff010000,
vmiop_log: error: 0xcaf00004, 0x0
vmiop_log: error: Timeout occurred, reset initiated.
Version
Citrix Hypervisor 6.2
Fix
Ensure that you are running the latest OEM firmware for your NVIDIA vGPU software boards.
Status
Closed
Ref. #
NVIDIA-327/1632120
6.47. Windows VM BSOD when upgrading NVIDIA drivers over a Citrix Virtual Apps and Desktops session
Description
Windows VM bugchecks when NVIDIA guest drivers are upgraded over a Citrix Virtual Apps and Desktops session.
If the VM is restarted after the bugcheck, the upgraded driver loads correctly and full functionality is available.
Fix
Upgrade Citrix Virtual Apps and Desktops to 7.6 Feature Pack 3
Status
Closed
Ref. #
NVIDIA-370/200130780
6.48. XenCenter does not allow vGPUs to be selected as a GPU type for Linux VMs
Description
When creating a new Linux VM or editing the properties of an existing Linux VM, XenCenter does not allow vGPUs to be selected as a GPU type.
vGPU on Linux VMs is supported as a technical preview on Citrix Hypervisor 6.5, and does include XenCenter integration.
Version
Affects the XenCenter integration with Citrix Hypervisor 6.5 only.
Resolved in the XenCenter integration with Citrix Hypervisor 7.0.
Workaround
Refer to XenServer vGPU Management in Virtual GPU Software User Guide for how to configure vGPU by using the xe CLI.
Status
Closed
Ref. #
NVIDIA-360
6.49. If X server is killed on a RHEL7 VM running vGPU, XenCenter console may not automatically switch to text console
Description
If X server is killed on a RHEL7 VM running vGPU, XenCenter console may display a corrupted image and fail to switchover to text console.
The failure to switchover to text console is due to a bug in RHEL7, which causes X server to not start correctly under certain configurations.
Workaround
Use CTRL+ALT+F1, F2, or F3 to switch between Linux terminals.
Status
Closed
Ref. #
NVIDIA-350/200123378
6.50. Citrix Virtual Apps and Desktops shows only a black screen when connected to a vGPU VM
Description
Citrix Virtual Apps and Desktops sometimes displays only a black screen when it is connected to an NVIDIA vGPU VM. The probable cause is that the display that is connected to the NVIDIA vGPU is entering a lower power state.
Fix
Disable all display-related power management settings.
For detailed instructions, visit Microsoft power plans frequently asked questions and from the list, select your OS version.
Status
Not an NVIDIA bug
Ref. #
1719877
Notice
This document is provided for information purposes only and shall not be regarded as a warranty of a certain functionality, condition, or quality of a product. NVIDIA Corporation (“NVIDIA”) makes no representations or warranties, expressed or implied, as to the accuracy or completeness of the information contained in this document and assumes no responsibility for any errors contained herein. NVIDIA shall have no liability for the consequences or use of such information or for any infringement of patents or other rights of third parties that may result from its use. This document is not a commitment to develop, release, or deliver any Material (defined below), code, or functionality.
NVIDIA reserves the right to make corrections, modifications, enhancements, improvements, and any other changes to this document, at any time without notice.
Customer should obtain the latest relevant information before placing orders and should verify that such information is current and complete.
NVIDIA products are sold subject to the NVIDIA standard terms and conditions of sale supplied at the time of order acknowledgement, unless otherwise agreed in an individual sales agreement signed by authorized representatives of NVIDIA and customer (“Terms of Sale”). NVIDIA hereby expressly objects to applying any customer general terms and conditions with regards to the purchase of the NVIDIA product referenced in this document. No contractual obligations are formed either directly or indirectly by this document.
NVIDIA products are not designed, authorized, or warranted to be suitable for use in medical, military, aircraft, space, or life support equipment, nor in applications where failure or malfunction of the NVIDIA product can reasonably be expected to result in personal injury, death, or property or environmental damage. NVIDIA accepts no liability for inclusion and/or use of NVIDIA products in such equipment or applications and therefore such inclusion and/or use is at customer’s own risk.
NVIDIA makes no representation or warranty that products based on this document will be suitable for any specified use. Testing of all parameters of each product is not necessarily performed by NVIDIA. It is customer’s sole responsibility to evaluate and determine the applicability of any information contained in this document, ensure the product is suitable and fit for the application planned by customer, and perform the necessary testing for the application in order to avoid a default of the application or the product. Weaknesses in customer’s product designs may affect the quality and reliability of the NVIDIA product and may result in additional or different conditions and/or requirements beyond those contained in this document. NVIDIA accepts no liability related to any default, damage, costs, or problem which may be based on or attributable to: (i) the use of the NVIDIA product in any manner that is contrary to this document or (ii) customer product designs.
No license, either expressed or implied, is granted under any NVIDIA patent right, copyright, or other NVIDIA intellectual property right under this document. Information published by NVIDIA regarding third-party products or services does not constitute a license from NVIDIA to use such products or services or a warranty or endorsement thereof. Use of such information may require a license from a third party under the patents or other intellectual property rights of the third party, or a license from NVIDIA under the patents or other intellectual property rights of NVIDIA.
Reproduction of information in this document is permissible only if approved in advance by NVIDIA in writing, reproduced without alteration and in full compliance with all applicable export laws and regulations, and accompanied by all associated conditions, limitations, and notices.
THIS DOCUMENT AND ALL NVIDIA DESIGN SPECIFICATIONS, REFERENCE BOARDS, FILES, DRAWINGS, DIAGNOSTICS, LISTS, AND OTHER DOCUMENTS (TOGETHER AND SEPARATELY, “MATERIALS”) ARE BEING PROVIDED “AS IS.” NVIDIA MAKES NO WARRANTIES, EXPRESSED, IMPLIED, STATUTORY, OR OTHERWISE WITH RESPECT TO THE MATERIALS, AND EXPRESSLY DISCLAIMS ALL IMPLIED WARRANTIES OF NONINFRINGEMENT, MERCHANTABILITY, AND FITNESS FOR A PARTICULAR PURPOSE. TO THE EXTENT NOT PROHIBITED BY LAW, IN NO EVENT WILL NVIDIA BE LIABLE FOR ANY DAMAGES, INCLUDING WITHOUT LIMITATION ANY DIRECT, INDIRECT, SPECIAL, INCIDENTAL, PUNITIVE, OR CONSEQUENTIAL DAMAGES, HOWEVER CAUSED AND REGARDLESS OF THE THEORY OF LIABILITY, ARISING OUT OF ANY USE OF THIS DOCUMENT, EVEN IF NVIDIA HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. Notwithstanding any damages that customer might incur for any reason whatsoever, NVIDIA’s aggregate and cumulative liability towards customer for the products described herein shall be limited in accordance with the Terms of Sale for the product.
VESA DisplayPort
DisplayPort and DisplayPort Compliance Logo, DisplayPort Compliance Logo for Dual-mode Sources, and DisplayPort Compliance Logo for Active Cables are trademarks owned by the Video Electronics Standards Association in the United States and other countries.
HDMI
HDMI, the HDMI logo, and High-Definition Multimedia Interface are trademarks or registered trademarks of HDMI Licensing LLC.
OpenCL
OpenCL is a trademark of Apple Inc. used under license to the Khronos Group Inc.
Trademarks
NVIDIA, the NVIDIA logo, NVIDIA GRID, NVIDIA GRID vGPU, NVIDIA Maxwell, NVIDIA Pascal, NVIDIA Turing, NVIDIA Volta, GPUDirect, Quadro, and Tesla are trademarks or registered trademarks of NVIDIA Corporation in the U.S. and other countries. Other company and product names may be trademarks of the respective companies with which they are associated.