BIOS Configuration
BMC supports configuring the NVIDIA® BlueField®'s BIOS using Redfish commands.
curl -k -u root:'<password>' -X GET https://<bmc_ip>/redfish/v1/Registries/BiosAttributeRegistry/BiosAttributeRegistry
Output example:
In the following output, there is only one BIOS attribute, UefiPassword.
{
"@odata.type": "#AttributeRegistry.v1_3_6.AttributeRegistry",
"Description": "This registry defines a representation of BIOS attribute instances",
"Id": "BiosAttributeRegistry",
"Language": "en",
"Name": "BF2 BIOS Attribute Registry",
"OwningEntity": "NVIDIA BlueField",
"RegistryEntries": {
"Attributes": [
{
"AttributeName": "UefiPassword",
"CurrentValue": "",
"DisplayName": "New UEFI Password",
"DisplayOrder": 16,
"HelpText": "Set the UEFI password.",
"Hidden": false,
"Immutable": false,
"MaxLength": 50,
"MenuPath": "./SystemConfiguration/UefiPassword",
"MinLength": 0,
"ReadOnly": false,
"ResetRequired": false,
"Type": "String",
"WriteOnly": false
}
],
"Dependencies": [],
"Menus": [
{
"DisplayName": "Set the UEFI Password.",
"DisplayOrder": 18,
"Hidden": false,
"MenuName": "UefiPassword",
"MenuPath": "./SystemConfiguration/UefiPassword",
"ReadOnly": false
}
]
},
"RegistryVersion": "1.0.0",
"SupportedSystems": [
{
"FirmwareVersion": "BlueField:4.2.0-33-gbe969d4",
"ProductName": "NVIDIA BF2",
"SystemId": "BF2-DPU"
}
]
}
curl -k -u root:'<password>' -H Content-Type: application/octet-stream -X GET https://<bmc_ip>/redfish/v1/Systems/Bluefield/Bios/
Output example:
The current value of UefiPassword is an empty string.
{
"@Redfish.Settings": {
"@odata.type": "#Settings.v1_3_5.Settings",
"SettingsObject": {
"@odata.id": "/redfish/v1/Systems/Bluefield/Bios/Settings"
}
},
"@odata.id": "/redfish/v1/Systems/Bluefield/Bios",
"@odata.type": "#Bios.v1_2_0.Bios",
"Actions": {
"#Bios.ChangePassword": {
"target": "/redfish/v1/Systems/Bluefield/Bios/Actions/Bios.ChangePassword"
},
"#Bios.ResetBios": {
"target": "/redfish/v1/Systems/Bluefield/Bios/Actions/Bios.ResetBios"
}
},
"Attributes": {
"UefiPassword": ""
},
"Description": "BIOS Configuration Service",
"Id": "BIOS",
"Name": "BIOS Configuration",
"ResetBiosToDefaultsPending": false
}
curl -k -u root:'<password>' -X PATCH https://<bmc_ip>/redfish/v1/Systems/Bluefield/Bios/Settings -d '{Attributes:{<attribute Name> : <attribute Value>}}'
This command example requests changing the UefiPassword attribute to NewPassword123. At the next boot cycle of the DPU, the UEFI changes the requested attribute if the requested value is valid.
curl -k -u root:'<password>' -X GET https://<bmc_ip>/redfish/v1/Systems/Bluefield/Bios/Settings
Pending values are a list of values that that user has requested to change. The list of pending values is purged once the UEFI changes the pending attributes.
Output example:
UefiPassword appears in the pending attributes list.
{
"@odata.id": "/redfish/v1/Systems/Bluefield/Bios/Settings",
"@odata.type": "#Bios.v1_2_0.Bios",
"Attributes": {
"UefiPassword": "NewPassword123"
},
"Description": "BIOS Settings",
"Id": "BIOS_Settings",
"Name": "BIOS Configuration"
}
The active BIOS attribute list is updated only after the UEFI approves the changes during the next reboot cycle.
Changing Default UEFI Password Using Redfish
Check the UEFI attributes and their values by performing a GET on BIOS URL over 1GbE OOB to the DPU BMC.
Look for the "Attributes" property to make sure the UEFI version being used has all the necessary attributes. See section "Get BIOS Attributes List" for instructions.
Perform PATCH to BIOS pending settings URI over 1GbE OOB to the DPU BMC as follows:
curl -k -X PATCH -d '{"Attributes":{"CurrentUefiPassword": "CURRENTPASSWD", "UefiPassword": "NEWPASSWORD"}}' -u root:<password> https://<DPU-BMC-IP>/redfish/v1/Systems/<SystemID>/Bios/Settings | python3 -m json.tool
To confirm whether the PATCH request completed successfully, trigger a GET to the BIOS pending settings URI over 1GbE OOB to the DPU BMC:
curl -k -X GET -u root:<password> https://<DPU-BMC-IP>/redfish/v1/Systems/<SystemID>/Bios/Settings | python3 -m json.tool
Reboot the DPU using the Redfish manager schema over 1GbE OOB to the DPU BMC. See section "Reboot BMC Redfish Command" for instructions.
If the "CurrentUefiPassword" is correct, then the UEFI password is updated during the UEFI Redfish phase of the boot.
Changing UEFI Password
curl -k -u root:<password> -X PATCH -H "Content-Type: application/json" https://<bmc_ip>/redfish/v1/Systems/Bluefield/Bios/Settings -d '{"Attributes":{"CurrentUefiPassword":"CurrentPassword", "UefiPassword":"NewPassword321"}}'
Viewing Currently Installed BIOS CA Certificates
The certificates installed on the UEFI may differ from the certificate presented on the DPU BMC. This discrepancy arises from a distinct certificate validation processed implemented in the UEFI and DPU BMC.
Trigger the following GET request to view the content of the system's Truststore:
curl -k -u root:<password> -X GET https:
//<bmc_ip>/redfish/v1/Systems/Bluefield/Oem/Nvidia/Truststore/CertificatesFor example, the following is the response when there are two certificates installed:
{
"@Redfish.SupportedCertificates": ["PEM"],"@odata.id":"/redfish/v1/Systems/Bluefield/Oem/Nvidia/Truststore/Certificates","@odata.type":"#CertificateCollection.CertificateCollection","Members": [ {"@odata.id":"/redfish/v1/Systems/Bluefield/Oem/Nvidia/Truststore/Certificates/1"}, {"@odata.id":"/redfish/v1/Systems/Bluefield/Oem/Nvidia/Truststore/Certificates/2"} ],"Members@odata.count":2,"Name":"TruststoreBios Certificate Collection"}Trigger the following GET request to view the details of a specific certificate:
curl -k -u root:<password> -X GET https:
//<bmc_ip>/redfish/v1/Systems/Bluefield/Oem/Nvidia/Truststore/Certificates/<cert_num>For example:
{
"@odata.id":"/redfish/v1/Systems/Bluefield/Boot/Certificates/1","@odata.type":"#Certificate.v1_7_0.Certificate","CertificateString":"<cert_str>","CertificateType":"PEM","Id":"1","Issuer": {"City":"Santa Clara","CommonName":"Kg639IcpJtYMRzvh.nvidia","Country":"US","Organization":"NVIDIA","OrganizationalUnit":"NBU","State":"California"},"KeyUsage": ["CRLSigning"],"Name":"TruststoreBios Certificate","Subject": {"City":"Santa Clara","CommonName":"Kg639IcpJtYMRzvh.nvidia","Country":"US","Organization":"NVIDIA","OrganizationalUnit":"NBU","State":"California"},"UefiSignatureOwner":"<UEFI_Owner>","ValidNotAfter":"2043-01-01T00:00:00+00:00","ValidNotBefore":"2023-01-01T00:00:00+00:00"}
BIOS CA Certificates Collection Operations
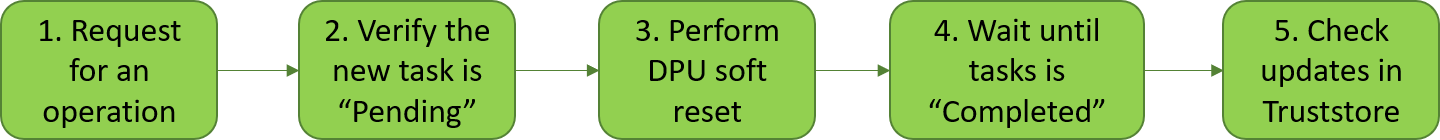
Request for an operation:
To install a certificate, trigger the following POST request which contains the certificate string and type in JSON format:
WarningThe BMC certificate must be replaced with a CA signed certificate before installing new CA certificates, and after BMC factory reset. See section "Example: CSR Generation, Certificate Creation and Replacement" for instructions.
ImportantIf an invalid certificate is installed, the BMC rejects it and does not display it. However, it is still accepted by the UEFI and it must be deleted manually through the UEFI menu.
curl -k -u root:<password> -X POST https://<bmc_ip>/redfish/v1/Systems/Bluefield/Oem/Nvidia/Truststore/Certificates -d @CAcert.json
The content of CAcert.json must be {"CertificateString": "<cert_string>", "CertificateType": "<cert_type>"}. Where:
cert_string – certification string which starts with -----BEGIN CERTIFICATE-----\n and ends with -----END CERTIFICATE-----\n.
WarningThe "\n" at the end are mandatory.
cert_type – certification type. Only "PEM" is supported.
To delete a CA certificate, trigger the following DELETE request with the CA certificate URI that should be deleted:
curl -k -u root:<password> -H "Content-Type: application/json" -X DELETE https://<bmc_ip>/redfish/v1/Systems/Bluefield/Oem/Nvidia/Truststore/Certificates/<cert_num>
To reset all certificates in the Truststore, trigger the following TruststoreCertificates.ResetKeys action with the DeleteAllKeys option:
curl -k -u root:<password> -H
"Content-Type: application/json"-X POST https://<bmc_ip>/redfish/v1/Systems/Bluefield/Oem/Nvidia/Actions/TruststoreCertificates.ResetKeys -d '{"ResetKeysType":"DeleteAllKeys"}'
Verify the new task is Pending:
The responses of these requests indicate the creation of a new task for the UEFI:
{ "@odata.id": "/redfish/v1/TaskService/Tasks/<task_id>", "@odata.type": "#Task.v1_4_3.Task", "Id": "<task_id>", "TaskState": "Pending", "TaskStatus": "OK" }
Perform DPU soft reset in order for the UEFI to start handling the pending tasks:
curl -k -u root:<password> -H "Content-Type: application/json" -X POST https://<bmc_ip>/redfish/v1/Systems/Bluefield/Actions/ComputerSystem.Reset -d '{"ResetType" : "GracefulRestart"}'
Wait until task is Completed.
The task details and status can be checked using the following GET request:
curl -k -u root:<password> -H "Content-Type: application/json" -X GET https://<bmc_ip>/redfish/v1/TaskService/Tasks/<task_id>
The task status can be either:
Pending – Initial state.
{
"@odata.id":"/redfish/v1/TaskService/Tasks/<task_id>","@odata.type":"#Task.v1_4_3.Task", ..."PercentComplete":0, ..."TaskState":"Pending","TaskStatus":"OK"}If the task remains in a "Pending" state after DPU reset completes, please check the UEFI-BMC communication.
In case of communication failure, consider either:Replacing the BMC certificate with one signed by a CA which its certificate was installed, and resetting DPU.
Removing all CA certificates from the UEFI menu.
Completed – Finished state.
{
"@odata.id":"/redfish/v1/TaskService/Tasks/<task_id>","@odata.type":"#Task.v1_4_3.Task", ..."PercentComplete":100, ..."TaskState":"Completed","TaskStatus":"OK"}Exception – Failure state.
{
"@odata.id":"/redfish/v1/TaskService/Tasks/<task_id>","@odata.type":"#Task.v1_4_3.Task", ..."PercentComplete":0, ..."TaskState":"Exception","TaskStatus":"OK"}In this case, verify that the certificate is valid.
Check updates in Truststore. See section "Viewing Currently Installed BIOS CA Certificates" for details.