The AIStore Authentication Server (AuthN) provides secure access to AIStore by leveraging JSON Web Tokens (JWT).
NOTE: AuthN is under development and has NOT gone through a complete security audit. Please review your deployment carefully and follow our security policy to report any issues.
COMPATIBILITY: Tokens issued with only the ‘username’ and ‘expires’ claims (deprecated in v4.2) will no longer pass AIS authentication in v4.3. New tokens will use ‘sub’ and ‘exp’ claims in place of ‘username’ and ‘expires’, respectively.
For more details:
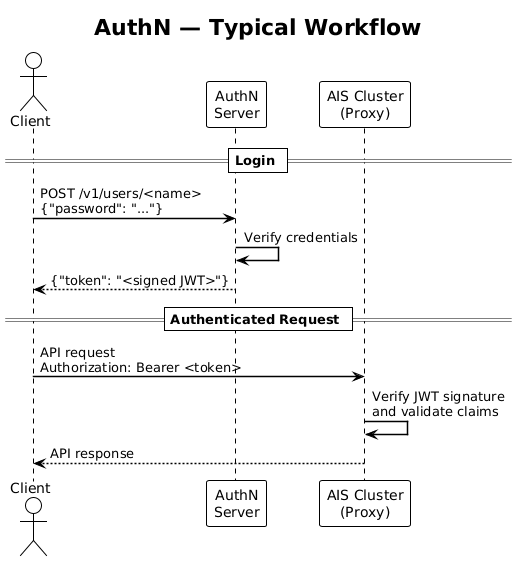
Authorization: Bearer <token>) for subsequent API requests to the AIStore cluster.AuthN supports both HTTP and HTTPS protocols.
By default, AuthN starts as an HTTP server listening on port 52001.
For HTTPS, ensure the configuration file options server_crt and server_key are correctly set to the TLS certificate and key paths.
AuthN generates tokens that are self-sufficient, meaning a proxy does not need to contact AuthN to check permissions. AIStore clusters should be registered with the AuthN server. This allows AuthN to broadcast revoked tokens to all registered clusters for immediate access restriction.
In this section, we use AIStore Local Playground. This is done for demonstration purposes, as it’s easy to use and reproduce.
If you already have an AIS cluster deployed and just want to add AuthN to it for authentication and access control, follow these instructions.
Note: When deploying AIStore with AuthN, an
adminuser is created by default withadminprivileges.The default password for the
adminuser must be set with the environment variableAIS_AUTHN_SU_PASS.For the list of environment variables, refer to the Environment Configuration section below.
Follow these steps to deploy a new local AIS cluster with AuthN enabled and RSA signing:
Optionally, shut down and clean up any existing Local Playground deployments and rebuild AIS CLI:
Build AuthN and deploy an AuthN server. The following example exports the required admin password. Then it runs AuthN with an auto-generated local config at $HOME/.config/ais/authn (see the deployment script). See key passphrase to optionally protect the private key on disk.
Fetch the public key from the AuthN service and export it for the AIS cluster to use:
Deploy the cluster with AuthN validation enabled:
This will start up an AIStore cluster that trusts JWTs issued by the AuthN server.
After deploying the cluster, you won’t be able to access it without authentication:
Log in as Admin:
View Registered Clusters:
Add Your Cluster:
Confirm Cluster Registration:
AuthN automatically deploys with a superuser role Admin and a user account admin with that role assigned.
Only users with the Admin role can manage AuthN.
Admins have superuser permissions and can assume all other roles in the cluster.
When a cluster is registered, AuthN creates a set of default roles for that cluster:
Ensure that you have auto-completions enabled for the AIS CLI:
You can use <TAB-TAB> to view a list of possible options:
Create a Bucket and Add an Object:
Create a Role and User:
For a comprehensive list of permissions, see the Permissions section below.
alice with this role:
Log in as the New User and Save the Token:
Perform Operations with Limited Permissions:
Further references:
The recommended and default signing method for AuthN-issued JWTs is RS256. This is an asymmetric signing system; the private key is managed solely by AuthN and never shared, while the public key is freely distributed.
The public key can be easily accessed in PEM format by simply running ais auth show public-key.
See auth_validation.md for info on configuring this for AIStore.
For dynamic public key lookup, see the OIDC issuer section below.
For production use, we recommend storing the generated private key on encrypted storage, e.g. a K8s secret.
The location of generated RSA private keys can be set with AIS_AUTHN_PRIVATE_KEY_FILE.
Otherwise, it defaults to a location in the config directory.
If this is not available or if you want additional protection, you can also protect the private key with a passphrase.
Set AIS_AUTHN_PRIVATE_KEY_PASS to use a passphrase for encrypting the key.
Note that this passphrase cannot be changed without replacing the key on disk.
While AuthN does not implement the full OIDC spec, it provides basic OIDC Discovery and JWKS endpoints. This allows an AIS cluster to trust tokens issued by AuthN without needing any static key details.
When configured with RSA signing, AuthN:
kid (key ID) header in every issued JWT/.well-known/openid-configuration/.well-known/jwks.json
The diagram below shows the authentication flow:
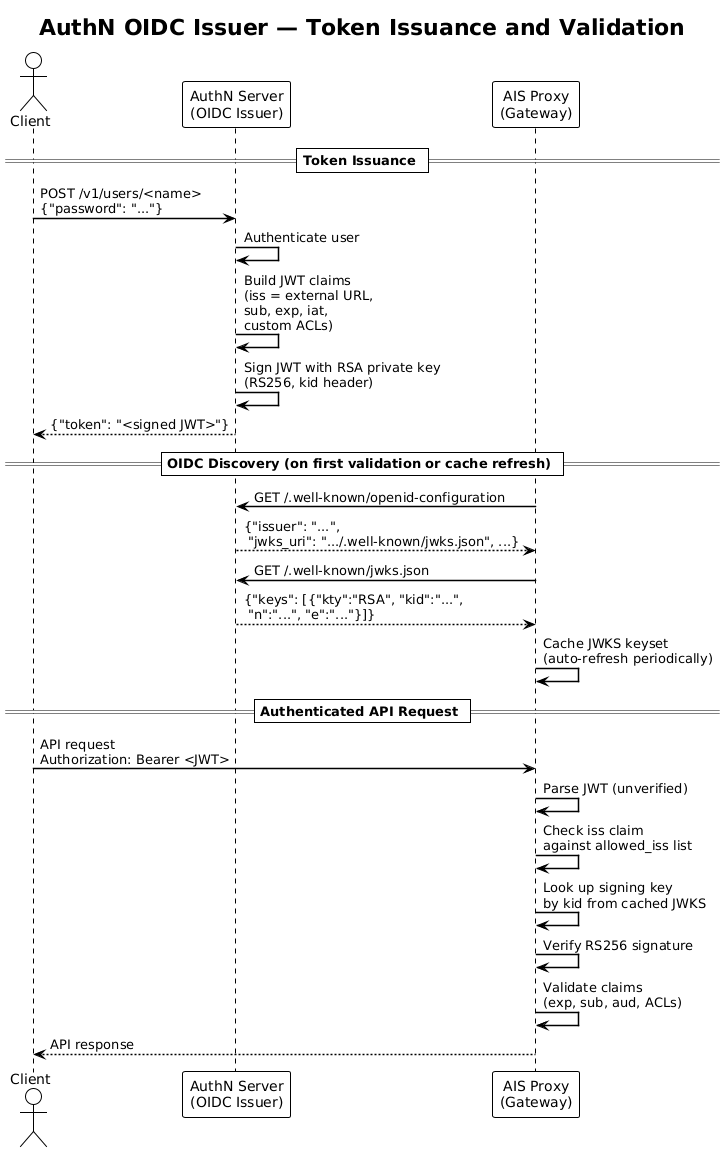
For details on configuring AIStore for validation based on OIDC lookup, see auth_validation.md.
AuthN must know its own externally reachable URL so that the OIDC discovery document and issued tokens contain the correct issuer value.
The iss claim in every token is set to this URL, and all endpoints in the discovery document are derived from it.
Set the external URL via the AIS_AUTHN_EXTERNAL_URL environment variable or the net.external_url field in authn.json:
If not set, AuthN defaults to http[s]://localhost:<port> (with a warning logged).
NOTE: In these examples we use
localhostas the hostname for the AuthN service. In a production deployment, this must be the hostname for the AuthN service accessible by AIStore. This can be provided by a load balancer, Docker network, K8s service, etc.
The external URL value must match an entry in auth.oidc.allowed_iss on the AIS cluster for OIDC validation to succeed.
Deploying with OIDC discovery simplifies the setup, but requires TLS for AuthN itself.
First, set up a self-signed certificate pair for localhost (see Generating self-signed certificates for a more complete example):
Then deploy both AuthN and AIStore locally with AuthN provisioned as a trusted OIDC issuer:
AIStore deploys before AuthN in this mode, so you can safely ignore warnings about key pre-caching failing. Once deployment is complete, AIStore will fetch the JWKS from AuthN as needed on the first validation.
Note: In this local deployment, both AuthN and the AIS cluster share the same TLS certificate (
AIS_SERVER_CRT/AIS_SERVER_KEY).AIS_SKIP_VERIFY_CRT=trueis set to accommodate the self-signed certificate. For production deployments, configureauth.oidc.issuer_ca_bundleinstead of skipping verification.
After deployment, configure the CLI to accept the self-signed certificate and set the HTTPS endpoint:
From here, follow the same Initial Setup and Authentication steps to log in, register the cluster, and create roles and users.
If asymmetric keys are not a requirement for your deployment, AuthN can still be used for basic access control with a single static HMAC secret used for both signing and validation.
Set AIS_AUTHN_SECRET_KEY to configure this for both AuthN signing and AIStore validation.
Note: The secret key used to validate tokens cannot be changed without restarting the cluster.
For variables used for AIStore token validation, see environment-vars.md.
Environment variables used by the AuthN server:
All variables can be set at AIStore cluster deployment and will override values in the config.
Separately, configure the following AuthN environment variables for client access:
Note: When AuthN is running, execute
ais auth show configto find out the current location of all AuthN files.
In AIStore, roles define the level of access by granting permissions to users. The available permissions are listed below:
The following values are provided as convenient aliases for a list of permissions:
By default, the AIStore deployment does not launch the AuthN server. To start the AuthN server manually, follow these steps:
Build AuthN:
Create a Configuration File:
Start the AuthN Server:
Start the AuthN server in a new terminal or screen session. Ensure that authn.json exists in the configuration directory.
Configure AIStore Cluster to Enable Token-Based Access:
Verify Access: Now, you cannot access the cluster without a token:
Log in as Admin: To continue operations, log in as the admin user:
Register the Cluster with AuthN: Register the AIStore cluster with AuthN to receive AuthN messages (e.g., revoked token list):
Proceed with Cluster Operations: After registering, you can proceed using your cluster with admin privileges. You can add users, set up roles, etc.
Note: This example assumes that AuthN is running on the same host as the AIS cluster. If AuthN is running on a different host, you will need to specify the
AIS_AUTHN_URLvariable. For example, useAIS_AUTHN_URL=http://10.10.1.190:52001 ais auth COMMAND.
In this section:
AUTHSRV- denotes a (hostname:port) address of a deployed AuthN server (default: http://localhost:52001)
Every request to AuthN (except login) must contain an authentication token in the header:
For curl, pass it as an argument: -H 'Authorization: Bearer token'.
See the auth validation doc for JWT claim requirements. In addition to meeting these requirements, tokens must also not be in the cluster’s revoked token collection.
AuthN ensures that all AIS gateways (proxies) are updated with each revoked token. When AuthN registers a new cluster, it sends the cluster the entire list of revoked tokens. Periodically, AuthN will clean up the list and remove expired and invalid tokens.
The example workflow below demonstrates the revocation process:
AIS Cluster 1 is registered with AuthNAIS Cluster 1 now rejects the previously valid tokenAIS Cluster 2 is not registered, so does not receive any revoked token listAIS Cluster 2 will still succeed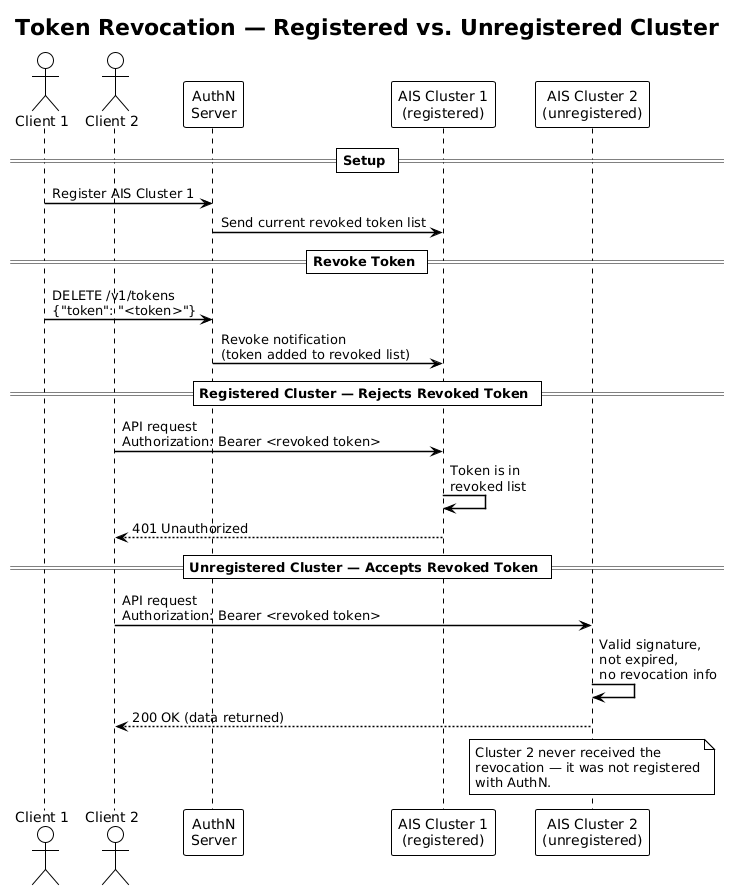
Generating a token for data access requires users to log in with a username and password.
By default, the token expiration time is set to 24 hours.
Modify expiration_time in the configuration file to change the default expiration time.
The maximum allowed token lifetime for a user to request can be configured with auth.max_token_age in the configuration file.
By default, this is set to 90 days and will disallow infinite tokens.
To issue a single token with a custom expiration time, pass an optional expiration duration in the request:
Pass a zero value with -e 0 to generate a token with the maximum allowed token lifetime, as configured by auth.max_token_age.
AuthN returns the generated token as JSON. Example: {"token": "issued_token"}.
The revoke token API shown below will forcefully invalidate a token before it expires.
When a cluster is registered, an arbitrary alias can be assigned to the cluster. The CLI supports both the cluster’s ID and the cluster’s alias in commands. The alias is used to create default roles for a newly registered cluster. If a cluster does not have an alias, the role names contain the cluster ID.
Note: A user can update their own password without admin privileges by issuing
PUT /v1/users/<user-id>with only thepasswordfield set, authorized with their own token. A user can also retrieve their own user info viaGET /v1/users/<user-id>using their own token.